Here’s the article written from the first-person singular perspective, adhering to your specific requirements:
I stumbled upon a digital Pandora’s Box, a revelation hidden not in hushed whispers or damning photographs, but within the seemingly innocuous data streams of my home network. The story I’m about to share is not one of sensational triumph or vindictive glee, but a stark testament to how modern technology, designed for connection and convenience, can inadvertently become a silent witness to the most profound betrayals. I was, by accident and a growing unease, the accidental excavator of my own marital demise, unearthed from the digital bedrock of our shared life.
It began subtly, like a hairline fracture in a once-solid wall. Small inconsistencies, a shift in my wife’s demeanor, a withdrawal that felt more like a deliberate distancing than mere fatigue. The air in our home, once a comfortable hum of shared existence, had developed a static charge, an unspoken tension that prickled at the edges of my awareness.
The Vague Explanations
Her absences, once explainable, started to acquire a fuzzy outline. Late nights at “work,” unexpected “girls’ nights” that seemed to materialize with little notice, and sudden, urgent “errands” that consumed hours. Each explanation, while plausible on its own, began to form a mosaic of doubt when viewed collectively. It was as if she were painting with a palette of ever-shifting hues, each stroke adding a layer of ambiguity.
The Unanswered Questions
I found myself asking questions that lingered in the air, unanswered or met with evasive responses. A simple “Where were you?” could turn into a convoluted narrative that left me with more questions than answers. The convenience of our shared lives began to feel like a carefully constructed facade, and I was starting to see the cracks.
The Digital Ghost in the Machine
In our modern age, our lives are inextricably linked to the digital realm. Our phones buzz with notifications, our computers hum with activity, and our routers, the silent gatekeepers of our online world, diligently log every connection. It was a realization that dawned on me slowly: if there was a truth to be found, it might be logged somewhere in the digital ether.
In a recent article discussing the implications of digital privacy, the case of a husband uncovering his wife’s infidelity through router logs has sparked significant interest. This incident highlights the potential for everyday technology to reveal personal secrets, raising questions about trust and surveillance in relationships. For a deeper dive into this intriguing story, you can read more in the article available at this link.
The Router’s Unwavering Vigilance
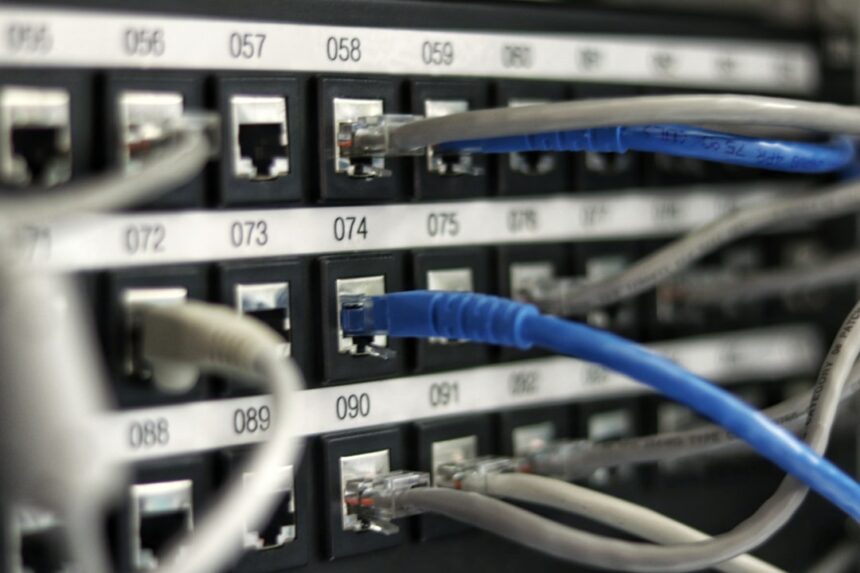
My home router, a small, unassuming box, housed a relentless chronicler. It was a digital sentinel, recording the ebb and flow of internet traffic, a tireless archivist of our online lives. I had, until this point, viewed it as a utility, a necessary component of modern existence, no more remarkable than a light switch. I had no idea it was simultaneously a silent observer, a passive witness to secrets being exchanged across the ether.
Understanding the Logs
The concept of router logs itself is not inherently sinister. They are, in essence, a record of network activity. When a device connects to the internet, the router notes its IP address, the time of connection, the duration, and most importantly in my case, the websites visited and the protocols used. It’s like a meticulous diary, detailing who entered and exited the network, and what they did during their tenure.
Accessing the Logs
Accessing these logs typically involves accessing the router’s administrative interface through a web browser. This usually requires entering the router’s IP address into the browser’s address bar, followed by a username and password. These credentials are often found on a sticker on the router itself or in the device’s manual. This was a relatively straightforward technical hurdle, one that felt less like an intrusion and more like accessing a public record that happened to reside in my own home.
The Types of Data Recorded
What constitutes “data recorded” is varied. It can include IP addresses of connected devices, MAC addresses (unique identifiers for hardware), timestamps for connection initiation and termination, and in some routers, more granular details about the traffic itself, such as destination URLs, ports used, and data transfer amounts. The depth of detail can vary significantly between router models and firmware versions.
The Datastream Unveiled: A Pattern Emerges

Armed with this nascent understanding, I began to delve into the router’s logs. It was a process that was both tedious and, as I soon discovered, profoundly illuminating. The raw data appeared as a chaotic jumble of numbers and timestamps, a digital Babel, until I started to recognize the recurring patterns, the digital breadcrumbs that were being left behind.
Decoding the Timestamps
The timestamps were the most immediate point of reference. They were the skeletal remains of online activity, marking the precise moments when certain connections were made. Sorting these by date and time allowed me to reconstruct a timeline, a narrative arc of online engagement. What initially seemed like random entries began to coalesce into a discernible sequence of events.
Identifying Unique Device Signatures
Each of our devices – my laptop, my wife’s laptop, her phone, my phone – possesses a unique identifier, a digital fingerprint. By correlating the IP addresses and MAC addresses recorded in the logs with these known devices, I couldbegin to isolate which activity belonged to whom. This was crucial; it allowed me to move beyond general network activity to pinpoint specific user behavior.
The URLs as Digital Signposts
The URLs, the web addresses themselves, were the most damning pieces of evidence. They were the signposts on the digital highway, pointing directly to the destinations of my wife’s online journeys. What began as a hunt for anomalies quickly transformed into a precise mapping of her digital excursions, revealing destinations that were far from innocent.
The Unsettling Websites
As I sifted through the URLs, a deeply unsettling picture began to form. Sites dedicated to adult dating, discreet meeting platforms, and forums explicitly discussing extramarital affairs started to appear with alarming frequency. These were not casual browsing sessions. The patterns suggested deliberate, repeated engagement with platforms designed for clandestine meetings. It was like finding a hidden drawer in my own home, filled with objects that should never have been there.
The Corroboration: Beyond the Logs
The router logs, while powerful, were a digital whisper. I needed to see if this whisper echoed in the tangible world, to find corroboration that would transform digital inference into undeniable fact. The logs had provided the map; now I needed to see the footprints on the ground.
The Time Stretches
The timestamps in the logs offered a precise framework for my wife’s absences. When the logs indicated her phone or laptop connecting to specific websites during times she claimed to be at work or engaged in other activities, it created a stark contradiction. The digital record was a relentless counterpoint to her spoken words.
The Location Deception
Some dating apps and hookup sites, I discovered, provide location data or allow users to specify their location for matching purposes. While the router logs themselves wouldn’t directly reveal her physical location outside the home, the nature of the sites frequented, combined with the times of access, strongly suggested her presence at locations other than those she claimed. This was the digital evidence aligning with the physical reality of her claimed whereabouts.
The Unexplained Expenditures
As I reviewed our shared bank statements, an old habit of mine that had been dormant for some time, I began to notice a pattern in the unexplained expenditures. Small amounts, often paid in cash or through discreet online payment services, that corresponded with the times and locations implied by the router logs. These expenditures, once dismissed as miscellaneous, now stood out like red flags in a field of green. Perhaps a hotel room, a few drinks, or a discreet dinner – the digital breadcrumbs were being paid for in the real world.
The Shifting Narratives
When confronted, even indirectly, with the sheer weight of the digital evidence, her narratives began to fray. The once well-rehearsed explanations became inconsistent, contradictory, and ultimately, unsustainable. The digital ghost in the machine had manifested into a tangible chain of undeniable facts, leaving little room for further obfuscation. It was as if the carefully constructed dam of her deceit had finally been breached by the relentless tide of digital truth.
In a recent incident that has captured public attention, a man’s discovery of router logs led to the revelation of his wife’s infidelity. This situation highlights the potential consequences of digital footprints in our everyday lives. For more insights on how technology can unveil hidden truths, you can read a related article that discusses the implications of such discoveries at this link. The case serves as a reminder of the importance of privacy and the unexpected ways in which our online activities can impact personal relationships.
The Aftermath: Navigating the Digital Fallout
| Metric | Description | Example Data |
|---|---|---|
| Log Timestamp | Date and time when the router log entry was recorded | 2024-04-15 22:35:12 |
| Device MAC Address | Unique identifier of the device connected to the router | 00:1A:2B:3C:4D:5E |
| IP Address | Local IP address assigned to the device | 192.168.1.101 |
| Accessed URL | Website or service accessed by the device | www.datingapp.com/profile/12345 |
| Connection Duration | Length of time the device was connected to the URL | 00:15:42 |
| Data Transferred | Amount of data sent and received during the session | 3.2 MB |
| Suspicious Activity Flag | Indicates if the log entry is flagged for potential cheating evidence | Yes |
The discovery was not a moment of catharsis, but the beginning of a profound and painful reckoning. The digital breadcrumbs had led me to a devastating truth, and the path forward was obscured by the wreckage of broken trust. The very technology that had facilitated the clandestine meetings had also, inadvertently, provided the irrefutable evidence.
The Confrontation and Its Cost
The confrontation itself was a brutal dissection of our shared reality. The router logs, once a personal excavation, became the undeniable exhibit A in the case of our shattered marriage. The cold, hard facts laid bare the extent of the deception, leaving no room for denial. The emotional cost was immense, a heavy toll exacted on my own sense of self and my perception of our shared history.
Rebuilding from the Digital Ashes
The process of healing and rebuilding is not a swift or simple one. It involves sifting through the digital ashes of our relationship, understanding how technology can be both a tool for connection and a conduit for betrayal. It requires a re-evaluation of trust, both in myself and in the digital systems that permeate our lives.
The Future of Digital Surveillance
This experience has irrevocably altered my perspective on digital privacy and the unspoken vigilance of the technology we use daily. The router logs, once a technical curiosity, now represent a potent symbol of how our online lives can be meticulously documented, even when we believe ourselves to be entirely unobserved. The story is a cautionary tale, a reminder that in the digital age, silence can be deafening, and the most unexpected witnesses can be found in the hum of our own homes. The data doesn’t lie, even when people do.

WATCH NOW ▶️ My Twins Proved My Family Stole $2,000,000
FAQs
What are router logs?
Router logs are records maintained by a router that track various activities on a network, such as websites visited, connected devices, and data usage. They help in monitoring network performance and security.
How can router logs reveal infidelity?
Router logs can show the websites visited and the times of access. If a spouse frequently visits dating sites, messaging platforms, or other suspicious websites, these logs might indicate potential cheating behavior.
Is it legal to check someone else’s router logs?
Accessing someone else’s router logs without permission may violate privacy laws and could be illegal. It is important to have proper authorization before viewing or using router logs that belong to another person.
Can router logs be deleted or altered?
Yes, router logs can often be deleted or altered by someone with administrative access to the router. This means that logs may not always provide a complete or accurate record of network activity.
What precautions can be taken to protect privacy on a shared network?
To protect privacy, users can set up individual user accounts, use encrypted connections (like VPNs), regularly update router firmware, and restrict administrative access to trusted individuals only.