I often find myself scrutinizing documents, not just for their textual content, but for the silent whispers they carry – the metadata. It’s a fascinating, almost clandestine world, where every digital interaction leaves an invisible impression, a ‘fingerprint’ that can reveal secrets the document’s creator never intended to share. My work often involves uncovering these metadata fingerprints, especially in the realm of forged documents, where their presence, or indeed their absence, can be a crucial piece of evidence. This article delves into how I approach this task, what I look for, and the profound implications of these digital breadcrumbs.
When I talk about metadata, I’m referring to “data about data.” It’s the descriptive information embedded within a digital file that isn’t the primary content itself, but rather provides context about that content. Imagine a physical painting; the content is the artwork, but the metadata would be the artist’s signature, the date it was painted, the canvas type, and perhaps even the gallery it was last exhibited in. In the digital realm, this concept explodes in complexity and detail.
The Unseen Layers of Information
Every time I create a document, save it, or even open it, a layer of metadata is typically generated or updated. This includes, but is not limited to, the creation date and time, the last modified date and time, the author of the document, the software used to create or edit it, and even the specific version of that software. For images, it can include camera make and model, GPS coordinates, exposure settings, and timestamps. It’s a rich tapestry of information, often overlooked by the casual observer.
Its Role in Disproving Authenticity
My primary interest in metadata, particularly in forged documents, lies in its ability to contradict the visible content. If a document purports to be from a certain date, but its metadata reveals a much more recent creation or modification date, a significant red flag is raised. It’s like finding a 17th-century painting signed with a 21st-century hand – an immediate indicator of potential forgery. The metadata acts as an independent witness, often more reliable than the document’s presented narrative.
In the realm of document verification, the concept of metadata fingerprints plays a crucial role in identifying forged documents. A related article that delves deeper into this topic can be found at this link, where the implications of metadata analysis in forensic investigations are explored. Understanding how metadata can reveal alterations and inconsistencies in documents is essential for professionals in law enforcement and legal fields.
Common Metadata Traces I Encounter
My investigative process typically begins with an exhaustive extraction of all available metadata. This can be a labor-intensive but rewarding endeavor, as different file types store metadata in varying formats and locations.
Microsoft Office Document Metadata (DOCX, XLSX, PPTX)
Microsoft Office files are particularly rich in metadata. When I examine these, I look for a wealth of information:
Author and Last Modified By Fields
These fields are often overlooked by an imposter. If a document is supposedly written by “John Doe,” but the “Last Modified By” field consistently points to “Jane Smith,” it’s a strong indicator of manipulation. I’ve seen cases where these fields reveal the true identity of the forger, despite their attempts to attribute the document to someone else.
Creation, Last Saved, and Total Editing Time
These timestamps and durations can tell a compelling story. A document claiming to have been meticulously crafted over several weeks, but showing a “Total Editing Time” of only a few minutes, suggests a rapid and perhaps superficial alteration. Conversely, a document claiming to be “brand new” with a creation date several years prior also raises suspicion. I often cross-reference these with the operating system file system timestamps, as these can sometimes be independently manipulated, but a discrepancy between the internal document metadata and the file system metadata is a strong anomaly.
Template Information and Hidden Text
Sometimes, a document is created from a template. The metadata can reveal the original template file name, which might be a corporate template, further solidifying or refuting the document’s alleged origin. Additionally, I meticulously search for hidden text, comments, and revision history. These elements are not always immediately visible but are integral parts of the metadata structure, often revealing earlier drafts or editorial notes that contradict the final presented version.
PDF Document Metadata (PDF)
PDFs are a cornerstone of digital document exchange, and consequently, a frequent target for forgery. Their metadata, while sometimes more consolidated, is equally crucial.
Producer and Creator Applications
The “Producer” and “Creator” fields in a PDF provide information about the software that generated the document. If a document is presented as an old, scanned document but the “Producer” field indicates a recent version of Adobe Acrobat, it’s a clear sign of digital manipulation. I’ve encountered documents supposedly originating from bespoke business systems that, upon metadata inspection, proved to be generic PDFs generated by common office software and then superficially edited.
Modification Dates and Linearization Status
Just like Office documents, PDF modification dates are critical. A PDF that hasn’t been “linearized” (optimized for fast web viewing) might indicate a more recent creation from an older source, as older PDF generators sometimes didn’t linearize by default. This is a subtle clue, but in combination with other factors, it can strengthen a case for forgery.
In the realm of document verification, understanding the intricacies of metadata fingerprints in forged documents is crucial for maintaining authenticity. A related article that delves deeper into this topic can be found at this link, where it explores various techniques used to detect alterations and the significance of metadata in identifying fraudulent activities. By examining these methods, professionals can better safeguard against the risks associated with document forgery.
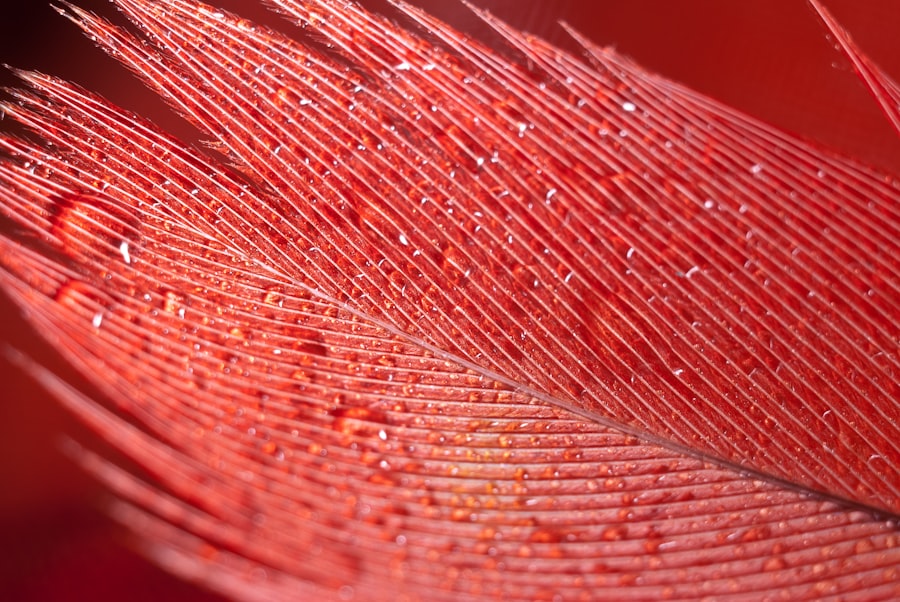
Image Files Metadata (EXIF, IPTC, XMP)
Images, particularly digital photographs, are incredibly rich in metadata, primarily through EXIF (Exchangeable Image File Format), IPTC (International Press Telecommunications Council), and XMP (Extensible Metadata Platform) tags.
Camera Make, Model, and Serial Number
This can be a definitive identifier. If an image is purported to be from a specific camera, but the EXIF data reveals a different make and model, the image’s authenticity is immediately called into question. In some high-stakes cases, even the camera’s unique serial number can be extracted, providing irrefutable proof of origin.
GPS Coordinates and Timestamps
The embedded GPS coordinates can be a powerful tool for corroboration or refutation. An image claiming to be taken in one location, but with GPS coordinates pointing to another, is an obvious red flag. Similarly, the capture timestamp, when compared to the alleged event time, can expose discrepancies. I often overlay these timestamps with known events or even weather patterns, creating a comprehensive picture.
Image Manipulation Software Signatures
When an image is altered using photo editing software, the software often leaves its own metadata signature. Detecting the presence of Photoshop, GIMP, or other editing suites can indicate that the image has been modified from its original state, even if the modifications are subtle. This doesn’t automatically mean forgery, but it necessitates a deeper dive into the pixel data for further anomalies.
My Methodical Approach to Metadata Analysis
To uncover these digital fingerprints, I employ a systematic approach that combines specialized tools with forensic expertise. It’s a delicate balance of automation and critical human interpretation.
Utilizing Specialized Forensic Tools
I rely on a suite of dedicated metadata extraction tools like ExifTool, Apache Tika, and various commercial forensic suites. These tools are designed to parse complex file structures and present the metadata in an organized, readable format. They allow me to delve into the deepest layers of a file, extracting even obscure tags that might hold vital information.
Cross-Referencing Internal and External Metadata
One of my core practices is to compare the internal metadata (that which is embedded within the document’s structure) with the external file system metadata (creation date, modification date, access date as recorded by the operating system). Discrepancies between these two layers are often indicative of manipulation. While file system timestamps can be more easily altered, inconsistencies between them and the ‘harder’ internal metadata are telling.
Historical Analysis of Metadata Timelines
I build a timeline of events based on the various timestamps found within the metadata. This includes creation, modification, last printed, and sometimes even save sequence numbers. A document’s metadata often tells a chronological story, and any breaks or illogical jumps in this timeline warrant a closer look. For instance, a creation date after a modification date is an impossibility in a genuine document.
Identifying Anomalies and Inconsistencies
The true art of metadata forensics, in my opinion, lies in spotting the anomalies. This isn’t just about finding data; it’s about discerning what doesn’t fit, what clashes with the presented narrative.
Contradictory Author Information
As mentioned before, author discrepancies are frequent. An individual claiming authorship of a document, yet consistently appearing in the “Last Modified By” field under a different name, is a classic example of an anomaly. I also examine if the author’s name changes midway through the document’s history, which could indicate a handover or, more sinisterly, an attempt to obscure the original creator.
Implausible Timestamps
Timestamps are a treasure trove of information. Dates and times that fall outside the reasonable scope of the alleged event, or that show signs of being reset (e.g., all timestamps aligning perfectly to a specific default time like Jan 1, 1970, or a system’s default reset time), are immediate red flags. I’ve even seen cases where timestamps were future-dated, clearly indicating an attempt to manipulate information.
Software Mismatches
If a document is presented as being from a specific, perhaps proprietary, software environment but its metadata indicates creation or modification by common readily available software, it’s a significant inconsistency. For example, a document claiming to be a bespoke engineering drawing but showing metadata from a generic word processor raises serious questions about its origin and authenticity. I also look for tell-tale signs of conversion processes; sometimes a document is genuinely created in one application, converted to another, and then allegedly forged. The metadata will still often carry the footprints of the original creation application.
The Challenges I Face and Their Solutions
While metadata is a powerful forensic tool, its analysis is not without challenges. Forgers are becoming more sophisticated, and I must continuously refine my techniques.
Metadata Stripping and Falsification
The most significant challenge I encounter is when individuals intentionally strip or falsify metadata. Tools exist specifically for this purpose, and a skilled forger can render a document largely devoid of its digital fingerprints.
The Absence as Evidence
In such cases, the very absence of metadata becomes a piece of evidence. A document that should, by its nature, contain a rich set of metadata (e.g., a photo taken with a modern smartphone or a complex Office document), but presents itself as completely sanitized, suggests an intentional act of concealment. This absence alone might not definitively prove forgery, but it significantly undermines the document’s credibility and points towards deliberate manipulation.
Recovering Deleted Metadata
Sometimes, even when metadata is “stripped,” remnants can still be recovered from unallocated clusters on a hard drive or by analyzing the file’s binary structure for previously embedded data that wasn’t completely overwritten. This is a more advanced technique, requiring significant forensic expertise and specialized software, but I always consider it a potential avenue for recovery.
Ethical and Legal Implications
My work with metadata always includes careful consideration of ethical and legal boundaries. The information I uncover can have profound consequences.
Privacy Concerns
Metadata can contain highly personal information, such as geographical locations, personal names, and even device serial numbers. I am always acutely aware of the privacy implications and ensure that my analysis is conducted within legal frameworks and ethical guidelines, focusing strictly on the evidentiary value related to the document’s authenticity.
Admissibility in Court
For metadata analysis to be effective, my findings must be admissible in court. This requires meticulous documentation of my methodology, chain of custody of the digital evidence, and an understanding of legal precedents regarding digital forensics. My reports must be clear, concise, and scientifically sound, capable of withstanding rigorous cross-examination. I must explain complex technical concepts in an understandable manner to a non-technical audience, presenting the metadata as an impartial witness.
In conclusion, my journey through the invisible layers of digital documents is a continuous exploration. Uncovering metadata fingerprints is not merely a technical exercise; it’s akin to archaeological excavation in the digital realm. Each timestamp, author field, or software signature is a shard of information, piecing together a narrative of creation, modification, and ultimately, authenticity. While forgers strive to erase their tracks, the digital world, by its very nature, tends to leave subtle yet indelible marks. My job is to find those marks, interpret their meaning, and let them speak their silent truth.

WATCH NOW ▶️ EXPOSED: The Smart Teddy Bear That Caught My Wife’s $2M Theft
FAQs
What are metadata fingerprints in the context of forged documents?
Metadata fingerprints refer to the unique digital traces embedded within a document’s metadata that can help identify its origin, creation process, and any alterations. In forged documents, these fingerprints can reveal inconsistencies or signs of tampering.
How can metadata fingerprints help detect forged documents?
By analyzing metadata fingerprints, experts can uncover discrepancies such as mismatched creation dates, unusual editing histories, or inconsistent software signatures. These anomalies often indicate that a document has been altered or forged.
What types of metadata are commonly examined in document forensics?
Commonly examined metadata includes creation and modification dates, author information, software used to create or edit the document, file format details, and embedded device information. These data points collectively form the metadata fingerprint.
Are metadata fingerprints reliable indicators of document authenticity?
While metadata fingerprints provide valuable clues, they are not foolproof. Skilled forgers may manipulate metadata to mimic authentic documents. Therefore, metadata analysis is typically combined with other forensic techniques for a comprehensive assessment.
What tools are used to analyze metadata fingerprints in forged documents?
Various forensic software tools and metadata analyzers, such as ExifTool, PDF Examiner, and specialized forensic suites, are used to extract and analyze metadata fingerprints. These tools help investigators identify inconsistencies and potential forgeries.