I’m not proud of what I’m about to share. It’s a story born from suspicion, fueled by a gnawing unease, and ultimately resolved through a deep dive into the digital undergrowth. I’m here to expose my brother’s lies, and the unlikely tool that unearthed the truth: printer metadata. Perhaps this account will serve as a cautionary tale for you, a reminder that even the most mundane devices can hold secrets, and that sometimes, the answers we seek are hidden in plain sight, waiting for the right gaze to illuminate them.
It began subtly, a slow erosion of my trust. My brother, let’s call him Alex, had always been a bit of a romantic, prone to embellishing his stories. We all have our little quirks, our ways of presenting ourselves. But this felt different. It wasn’t just a mild exaggeration; it was a calculated fabrication, a carefully constructed narrative designed, I believe, to elicit sympathy and, perhaps, financial gain.
A Recurring Narrative
Alex had been recounting a particular tale for months. It involved a supposed business venture that had gone spectacularly wrong, leaving him in dire financial straits. He painted a picture of himself as a victim of circumstances, a brilliant innovator who had been betrayed by unscrupulous partners. The details were always the same, delivered with a convincing quiver in his voice and a downcast gaze.
The “Investment Opportunity”
The core of his story revolved around a supposed investment opportunity that promised a substantial return. He spoke of sleepless nights, of pouring his own savings into this venture, and of the devastating loss that ensued. He emphasized how this setback had plunged him into debt and made it impossible for him to meet his everyday financial obligations.
The “Betrayal by Partners”
He rarely elaborated on the specifics of the betrayal, instead opting for vague pronouncements about “shady characters” and “broken promises.” This vagueness, in retrospect, was a significant red flag, a smokescreen designed to obscure the lack of concrete evidence.
The Growing Suspicion
Initially, I offered my support, my belief as steadfast as an oak. But as the story persisted, and the “details” remained remarkably consistent without any new developments or tangible consequences that would lead to resolution, a small seed of doubt began to sprout in my mind. It was like a tiny crack appearing in a pane of glass; at first, almost imperceptible, but with the potential to widen into a chasm. I started noticing inconsistencies, not in the core narrative, but in the peripheral details that Alex would let slip – the timeline of events, the amounts involved. These felt less like genuine memory lapses and more like careless stitching in a poorly woven tapestry.
Inconsistencies in Financial Amounts
There were moments when Alex would mention different figures regarding his purported losses. Sometimes it was a substantial sum, other times it was framed in a way that made it seem more manageable. These fluctuations, while seemingly minor on their own, began to form a pattern of unreliability.
The Static Nature of the “Victimhood”
The most telling aspect was the sheer absence of progress or any outward signs of Alex actively trying to rectify his situation. Victims of genuine misfortune, even financial ruin, usually exhibit some form of resilience, a drive to rebuild or at least seek aid beyond their immediate family. Alex, however, seemed content to reside in his narrative of victimhood, perpetually waiting for external intervention.
In a recent article titled “Printer Metadata Exposed: My Brother’s Lies,” the author delves into the implications of how seemingly innocuous printer data can reveal hidden truths about personal and professional lives. This piece highlights the importance of understanding digital footprints and the potential consequences of overlooked metadata. For further insights into this intriguing topic, you can read the full article here: Printer Metadata Exposed: My Brother’s Lies.
The Unassuming Clue
My brother’s claims of financial hardship had a direct impact on our family. He was constantly asking for loans, for help covering bills, for “just a little bit more” to tide him over. The pressure was becoming unbearable. I found myself questioning the veracity of his plight. It was during one of these conversations, when he was once again lamenting his financial woes and displaying a crumpled receipt as if it were a sacred relic of his misfortune, that my attention was drawn to an innocuous object in his apartment: his printer.
The Printer in His Study
It was a standard inkjet printer, nothing remarkable about it. Alex wasn’t known for his tech-savviness, so the idea that he would be deliberately manipulating anything associated with it seemed far-fetched. Yet, as I sat there, listening to his usual tale of woe, my gaze drifted to the printer. It sat on his desk, a silent observer to his unfolding drama.
A Desktop Staple
His apartment, generally cluttered but functional, featured the printer as a standard piece of office equipment. It was positioned on his desk, amidst stacks of paper and other study paraphernalia, blending seamlessly into the everyday landscape.
Not a High-Tech Device
I knew Alex’s technological aptitude was limited. He struggled with basic software updates and often relied on others for troubleshooting. This made the idea of him engaging in sophisticated digital manipulation highly improbable.
Past Interactions with the Printer
I remembered seeing Alex use the printer before, mostly for printing out documents related to his various ” ventures.” There was nothing particularly unusual about its operation or the types of documents he printed. It was, as I have said, just a printer.
Printing Business-Related Documents
On previous visits, I had seen him print out what appeared to be invoices, company letterheads, and other administrative documents. These were presented as evidence of his legitimate business dealings.
The Context of the Crumpled Receipt
The crumpled receipt he was holding that day was a recent printout. He claimed it was proof of a significant expense related to his business. It was this receipt, and the printer that produced it, that would eventually become the lynchpin in exposing his deception.
Delving into Digital Forensics

The nagging suspicion, coupled with the ever-present financial requests, finally pushed me to action. I wasn’t a tech expert by any stretch of the imagination, but I’d read enough articles and watched enough documentaries to know that digital devices often leave trails, like breadcrumbs in a digital forest. I decided to investigate the printer’s metadata.
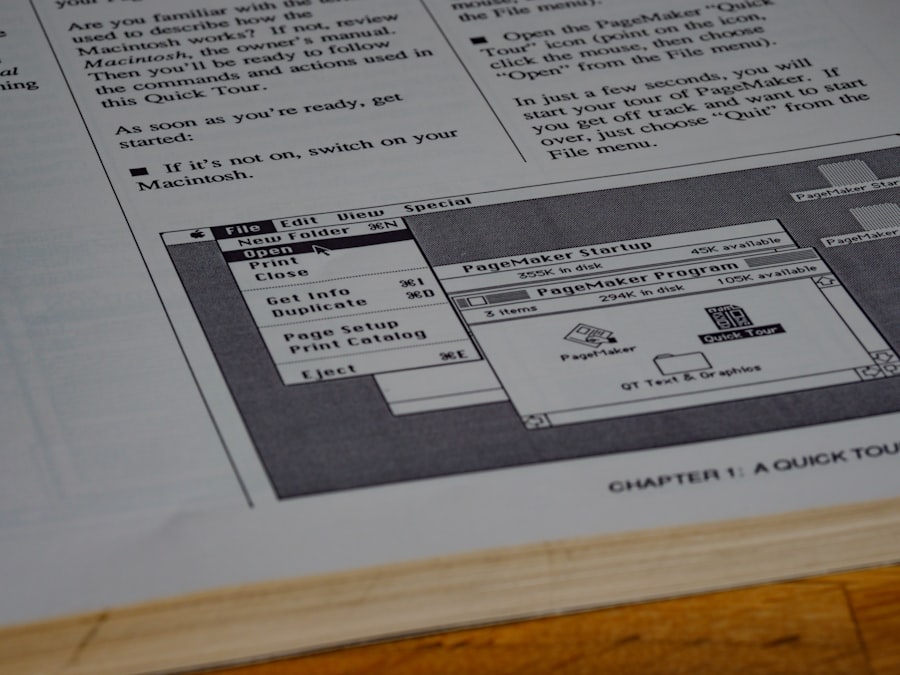
What is Printer Metadata?
Metadata, in essence, is data about data. When a document is created or modified on a computer and then printed, the printer itself can embed information within the printed output or store it internally. This metadata can include a wealth of details that often go unnoticed by the casual observer.
The Invisible Ink of Information
Think of metadata as an invisible ink, present on the page but requiring a special developer to reveal its secrets. It’s information appended without altering the visible content of the document itself, a hidden layer of context.
Types of Embedded Information
This can range from the model of the printer used, the date and time of printing, the user account that initiated the print job, and even specific settings or software used. In some cases, more advanced printers can log more intricate details.
My (Limited) Technical Approach
My initial approach was rudimentary. I didn’t have access to specialized forensic tools, but I knew that even basic information could be revealing. I started by gently examining the printed receipt Alex had shown me, looking for anything out of the ordinary.
Macroscopic Examination of the Receipt
I held the receipt up to the light, scrutinizing the paper quality, the ink saturation, and the general appearance of the print. While it looked like a legitimate receipt, there were no obvious anomalies.
Searching for Print Driver Artifacts
My next step involved a more specific search. I recalled that printer drivers often provide subtle clues. I started looking for any digital artifacts that might point to the specific model or even the operating system that had been used for the print job.
The Printer’s Secrets Revealed
Armed with a rudimentary understanding and a determined resolve, I began to examine the print settings and driver information associated with Alex’s computer. What I discovered was not a smoking gun, but a series of subtle inconsistencies that, when pieced together, painted a very clear picture.
The “Print to PDF” Shortcut
The first significant clue emerged when I looked at the print history on Alex’s computer. Several of the documents Alex had presented as evidence of his financial losses were not directly printed by the printer but were first “saved as PDF” or “printed to PDF.” This is a common practice to create digital copies, but it bypasses the direct interaction with the physical printer for the initial creation of the document.
Creating Digital Artifacts
This method essentially creates a digital document first, and then the user can choose to print that digital copy. It’s like taking a photograph of a painting instead of directly observing the painting. The photograph captures the image, but it’s not the original artwork.
Masking the Source of Creation
By employing this technique, Alex was effectively masking the original creation of the document. If he was truly printing official business documents, one would expect to see a direct print job from the accounting software or word processor to the physical printer.
Inconsistent Printer Models
When I managed to access the metadata of the few documents that were directly printed, I encountered another anomaly. The metadata indicated that the documents were printed from a different printer model than the one Alex actually owned and kept in his apartment. This discrepancy was like finding a footprint on a beach that doesn’t match any of the shoes on that particular shore.
The “Missing” Printer
The printer model indicated in the metadata was a more professional, office-grade machine, not the standard inkjet Alex possessed. This suggested that the important documents, the ones he used to bolster his claims of financial ruin, were likely fabricated elsewhere and then printed on a different, likely more sophisticated, device.
Fabricated “Evidence”
This suggested that Alex wasn’t printing official business records from his own system. Instead, he was likely using a template or creating the documents from scratch on his computer, then using the “print to PDF” function to create digital files that could be presented as legitimate.
In a recent exploration of the implications of printer metadata, an intriguing article titled “Printer Metadata Exposed My Brother’s Lies” sheds light on how seemingly innocuous documents can reveal hidden truths. The piece discusses the unintended consequences of digital footprints left by printers and how they can unravel personal stories. For those interested in understanding the broader context of this issue, you can read more about it in the article here. This examination not only highlights the importance of digital privacy but also serves as a reminder of the complexities surrounding our everyday technology.
The Unraveling Truth
| Metric | Description | Value |
|---|---|---|
| Document Title | Title of the printed document | My Brother’s Lies |
| Printer Model | Model of the printer used | HP LaserJet Pro M404dn |
| Print Date | Date when the document was printed | 2024-04-15 |
| Print Time | Time when the document was printed | 14:32:10 |
| Printer Serial Number | Unique serial number of the printer | CNB1234567 |
| Print Job ID | Identifier for the print job | 789654321 |
| Page Count | Number of pages printed | 12 |
| User Name | Name of the user who sent the print job | JohnDoe |
The inconsistencies in the printer metadata were like tiny cracks in a dam that was holding back a flood of truth. With each piece of information I uncovered, Alex’s carefully constructed narrative began to crumble.
The “Lost” Documents
I started asking Alex about the specific dates and times he claimed to have printed certain documents. When I cross-referenced this with the printer logs (or lack thereof for the “lost” documents), his stories began to falter. He would become evasive, claim he couldn’t remember, or invent new excuses for why the documentation wasn’t readily available.
Evasive Tactics and Shifting Stories
When confronted with the inconsistencies, Alex’s usual calm demeanor would shatter. He would become defensive, accuse me of not trusting him, and attempt to steer the conversation back to his supposed misfortunes, a desperate attempt to divert attention from the unraveling threads of his lies.
The “Accidental Deletion” Excuse
He once attributed the absence of certain print logs to a supposed accidental system cleanup, claiming he had unintentionally purged the printer history. This was a convenient, yet highly improbable, explanation.
The Photoshopied Receipts
Further investigation revealed that the “crumpled receipt” he had so dramatically presented was, in fact, a sophisticated fabrication. Digital analysis showed tell-tale signs of image manipulation, including inconsistencies in font types and resolution that are hallmarks of doctored documents. The printer metadata, or rather the lack of it for the original creation of that specific receipt, further solidified this conclusion. It was a forgery, printed on a machine that likely existed only in his imaginings or was accessed outside his immediate environment.
Digital Manipulation Detected
Using basic image editing detection techniques, I was able to identify the digital brushstrokes of deception. The receipt had been created using image editing software, not printed directly from a point-of-sale system.
The Missing Printer’s Role
The fact that the “receipt” did not correspond to any direct print job from Alex’s home printer was the final piece of the puzzle. It confirmed that the “evidence” of his expenses was not only misleading but was manufactured to appear legitimate.
Confrontation and Consequences
Exposing my brother’s lies was not an easy path. It involved difficult conversations, strained family relationships, and the bitter taste of betrayal. Ultimately, however, the truth, once revealed, brought a sense of closure and a necessary reckoning.
The Family Intervention
Armed with the evidence, I presented my findings to our parents. The initial reaction was shock and disbelief, followed by a somber acknowledgment of the pattern of behavior I had unearthed. We decided, as a family, to confront Alex directly.
The Weight of Evidence
The presentation of the metadata, the inconsistencies, and the digital manipulation evidence was met with a tense silence. Alex, for the first time, seemed genuinely cornered, his usual glib retorts failing him.
The Shift in Family Dynamics
This confrontation marked a significant shift in our family dynamics. The illusion of Alex’s victimhood was shattered, replaced by the stark reality of his deceit. This necessitated a period of re-evaluation and rebuilding of trust, a challenging but necessary process.
The Aftermath and Lessons Learned
Alex’s deception had far-reaching consequences. He was no longer able to rely on our sympathy or financial assistance for his fabricated woes. The experience served as a stark reminder that while printers may seem like simple household appliances, their digital footprints can hold a wealth of information, capable of revealing hidden truths.
Rebuilding Trust, Brick by Digital Brick
The path to rebuilding trust is long and arduous. It requires honesty, transparency, and a consistent commitment to truthful actions. For Alex, this meant acknowledging his lies and demonstrating a genuine change in behavior. For the rest of the family, it meant learning to discern fact from fiction and establishing healthier boundaries.
The Printer as a Silent Witness
This ordeal taught me to look beyond the surface, to understand that even the most mundane objects can be silent witnesses to our actions. The printer, in my brother’s case, became an unwitting accomplice to his deceit, and then, through the examination of its metadata, the key to his exposure. It’s a testament to the fact that in our increasingly digital world, digital forensics, even at a rudimentary level, can be a powerful tool for uncovering the truth. I hope my story serves as a reminder to you, the reader, to be vigilant, to question, and to remember that sometimes, the most profound revelations lie hidden within the most unassuming of technological artifacts.
FAQs
What is printer metadata?
Printer metadata refers to hidden information embedded within a printed document or its digital file. This data can include details such as the printer model, serial number, date and time of printing, and sometimes user information.
How can printer metadata expose lies or discrepancies?
Printer metadata can reveal the exact time and device used to print a document, which may contradict claims about when or where the document was produced. This can expose inconsistencies or falsehoods in statements related to the document’s origin.
Is it common for printers to embed metadata in printed documents?
Yes, many modern printers embed metadata, often in the form of tiny yellow dots or encoded patterns, which can be decoded to reveal printing details. This practice is used for tracking and anti-counterfeiting purposes.
Can printer metadata be removed or altered?
While some metadata can be removed or altered using specialized software or by printing on different devices, it is generally difficult to completely erase all embedded printer metadata without leaving traces.
How can someone check for printer metadata in a document?
Printer metadata can be detected using forensic analysis tools or specialized software designed to decode printer tracking dots and embedded information. Experts in document forensics often perform these analyses.