It’s a situation I wouldn’t wish on anyone. The gnawing suspicion, the sleepless nights, the slow erosion of trust. I’m talking about webcam fraud within the family, a betrayal that cuts deeper than most. It’s a complex issue, entangled with emotions and family dynamics, but for those who suspect it’s happening, establishing proof is crucial. This isn’t about witch hunts or baseless accusations; it’s about seeking clarity and potentially protecting loved ones from exploitation. I’ve navigated this murky territory, and I want to share what I’ve learned, not with a sense of triumph, but with a somber understanding of the challenges involved.
When I first started suspecting something was amiss, the term “webcam fraud” felt so clinical, so distant from the tangled web of my own family. It’s not just a simple scam; it can manifest in various insidious ways, often preying on vulnerability, loneliness, or a desire for connection. I needed to understand the different forms it could take to even begin to look for signs.
The Spectrum of Deception
It’s important to recognize that “webcam fraud” isn’t a monolith. It’s a broad category encompassing a range of deceptive practices that exploit the intimacy and perceived safety of online interactions.
Romance Scams: Building a False Intimacy
This is perhaps the most commonly understood form. Someone cultivates a romantic relationship through video calls, building emotional intimacy and trust. They present themselves as a genuine romantic interest, often with a fabricated backstory and compelling personal narrative. The goal is to eventually elicit money, gifts, or even private information under false pretenses. I saw how convincing these narratives could be, how carefully constructed the personas were.
The Gradual Escalation of Demands
The initial requests are often small, almost negligible – a few dollars for an emergency, a small gift to show affection. This is a deliberate strategy to test the waters and gauge the victim’s willingness to comply. As trust deepens, the demands escalate, becoming more significant and urgent. I learned that the money rarely goes to the stated purpose.
Exploiting Emotional Vulnerability
These scammers are adept at identifying and exploiting emotional vulnerabilities. Loneliness, recent loss, or a desire for companionship can all be fertile ground for these predators. They offer exactly what the victim craves – attentive conversation, romantic gestures, and a projected future – making it incredibly difficult to disconnect.
Sextortion and Blackmail: The Threat of Exposure
This form of fraud leverages compromising material obtained through webcam interactions. The perpetrator might secretly record a private conversation or a sexually explicit act and then use this material to extort money or favors from the victim. The threat of exposing this content to friends, family, or even employers creates immense pressure.
The Digital Footprint of Compromise
Any interaction where private or intimate details are shared via webcam carries a risk. The ease with which screen recordings can be made, even without the victim’s knowledge, is a chilling reality. I had to consider the possibility that seemingly innocent interactions could be weaponized later.
The Fear of Reputational Damage
The core of sextortion lies in the victim’s fear of shame, embarrassment, and the potential damage to their reputation. This fear is a powerful motivator, and the perpetrators exploit it ruthlessly. The thought of loved ones seeing such content is a potent weapon.
Impersonation and Identity Theft: Trading on Trust
In some cases, individuals might use webcam interactions to impersonate someone known to the family, or to gather enough personal information to facilitate identity theft. This could involve posing as a relative in distress, a trusted friend, or even a financial advisor.
The Familiar Facade
Seeing a familiar face can disarm caution. Scammers might use deepfake technology or simply have a convincing enough impersonation. However, often they’re simply exploiting existing relationships and a victim’s willingness to believe someone they “know.”
Information Extraction for Malicious Purposes
Beyond financial gain, the information gleaned through these interactions can be used for a variety of malicious purposes. This could include gaining access to sensitive accounts, planting misinformation, or even facilitating further exploitation of other family members.
Recognizing the Red Flags: Subtle Shifts in Behavior
The initial signs are often subtle, easily dismissed as oddities or temporary idiosyncrasies. It was the accumulation of these subtle shifts that eventually led me to investigate further. It’s not about a single dramatic event, but a pattern that emerges over time.
Uncharacteristic Financial Demands
This is a significant red flag, especially if the requests are for large sums, sent through unusual channels, or if the explanations seem vague or inconsistent. I learned to scrutinize any sudden need for money, particularly if it’s a recurring theme.
The “Emergency” Ruse
Frequent “emergencies” that require immediate financial intervention are a classic tactic. These emergencies often involve elaborate stories of illness, legal trouble, or travel complications.
Shifting Payment Methods
A sudden insistence on using gift cards, wire transfers, or cryptocurrency for payments can be a warning sign, as these methods are harder to trace.
Secrecy or Evasiveness Regarding Online Activity
If a family member becomes unusually secretive about their online communications, especially when using webcams, it’s cause for concern. This could manifest as suddenly closing their laptop when someone enters the room, being vague about who they’re talking to, or refusing to show their screen.
The Sudden Change in Privacy Habits
A person who was once open about their online interactions might become guarded, creating new passwords without explanation, or deleting chat histories.
Avoiding Direct Communication with Other Family Members
If the suspected fraudulent activity creates a barrier, the individual might avoid open communication with other family members about their online life.
Noticeable Emotional or Behavioral Changes
The stress and manipulation involved in webcam fraud can take a toll on a person’s emotional and mental well-being. I observed changes in mood, increased anxiety, withdrawal, or uncharacteristic irritability.
Increased Stress and Anxiety
The pressure of maintaining a deception or being manipulated can lead to visible signs of stress and anxiety.
Withdrawal and Isolation
As the manipulative relationship intensifies, the individual might withdraw from other family relationships, preferring to spend more time online.
If you suspect that a family member has used a budget webcam for fraudulent activities, it is essential to gather evidence to support your claims. A related article that can provide valuable insights on this topic is available at this link. This resource outlines various methods for identifying the use of low-cost technology in scams and offers guidance on how to document your findings effectively. By following the suggestions in the article, you can build a stronger case and take appropriate action.
Gathering Evidence: The Detective Work
When I started my investigation, the thought of “gathering evidence” felt cold and clinical. But I realized that without concrete proof, my suspicions would remain just that – suspicions, fueling further conflict and distrust. This isn’t about spy movies; it’s about meticulous observation and documentation.
Documenting Communications: The Written Record
The digital trail is often the most accessible and reliable form of evidence. It’s essential to systematically collect any communication that seems suspicious, be it emails, text messages, or chat logs.
Saving Chat Logs and Messages
Many platforms allow users to save or export chat histories. If I suspected a specific platform was being used, I’d look for ways to preserve those conversations. This involved taking screenshots or, if possible, exporting the entire chat log.
Timestamps and Content Preservation
It’s crucial to ensure that timestamps are visible in any saved communications. The content itself, with all its nuances, is paramount. I learned to look for inconsistencies in language, tone, or the narrative being presented.
Preserving Emails and Voicemails
Emails and voicemails can offer further context and corroboration. If an individual is receiving emails from unknown senders or consistent voicemails that seem to originate from a scammer, these need to be saved.
Archiving Suspicious Correspondence
Any email with unusual requests, suspicious links, or a tone that doesn’t align with known contacts should be archived. The same applies to voicemails that are vague, urgent, or contain a plea for money.
Cross-Referencing with Other Communications
The power of this evidence lies in its ability to corroborate other suspicious interactions. If a chat log mentions a specific request, and an email details that same request, the evidence becomes stronger.
Observing Financial Transactions: Tracing the Money Trail
Money is often the ultimate objective of these scams, making financial records a critical piece of evidence.
Reviewing Bank Statements and Credit Card Bills
I looked for any unusual or unexplained withdrawals, transfers, or purchases that coincided with the suspected fraudulent activity. This often meant scrutinizing credit card statements for online purchases that didn’t make sense.
Identifying Patterns of Transaction
A consistent pattern of sending money to unfamiliar accounts or individuals is a significant red flag. I tried to see if there was a regular outflow of funds that couldn’t be accounted for.
Tracing Remittances and Wire Transfers
If money was sent via wire transfer or other remittance services, I’d look for records of these transactions. These often provide detailed information about the recipient.
Examining Gift Card Purchases and Cryptocurrency Transactions
These are favored methods for scammers due to their anonymity. Observing a pattern of purchasing unusual quantities or denominations of gift cards, or frequent cryptocurrency transactions to unknown wallets, is highly suspicious.
The Anonymous Exchange
The lack of traceable identities in these transactions makes them a powerful tool for fraudsters. I had to be vigilant about any sudden interest in these payment methods.
Correlating with Communication
It was important to link these financial activities with specific communications or requests made during webcam interactions. This provided the context for why these transactions were occurring.
Digital Forensics: When to Call in the Professionals
For complex cases, or when direct evidence is difficult to obtain, digital forensics can be invaluable. I didn’t have the expertise for this, so I knew I’d need help.
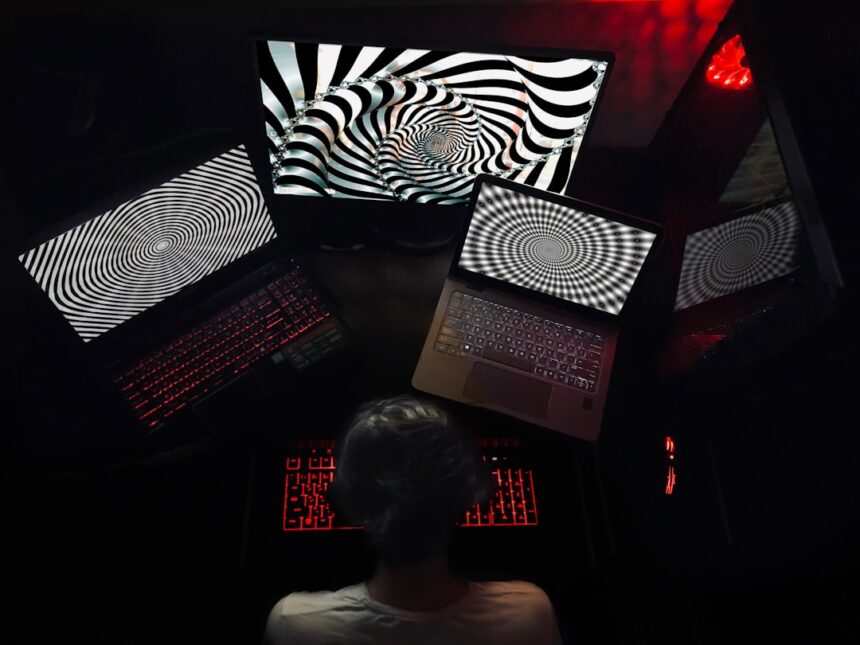
Screen Recording and Capture Tools
If there’s consent (or in situations where legal grounds exist and are advised by counsel), screen recording software can capture actual webcam interactions. This is a delicate area and requires careful consideration of privacy laws.
Documenting the Actual Interaction
This is the most direct form of evidence, showing exactly what transpires during a webcam call. However, ethical and legal considerations are paramount here.
Data Recovery and Analysis
In some instances, deleted data from a device might contain crucial evidence of fraudulent activity. Professional data recovery services can sometimes retrieve this information.
Understanding What Was Deleted
The ability to recover deleted messages, call logs, or even browsing history can paint a clearer picture of what transpired.
Expert Interpretation of Digital Artifacts
Digital forensics experts can analyze the metadata and digital artifacts on a device to piece together a timeline of events and identify any signs of manipulation or unauthorized access.
Navigating the Emotional Minefield: The Impact on Family Bonds

This isn’t just about gathering facts; it’s about dealing with the emotional fallout. Accusations, even when substantiated, can fracture relationships. I had to prepare myself for this.
Confrontation: A Delicate Dance
Confronting a family member about suspected webcam fraud is perhaps the most challenging aspect. It requires careful planning, a calm demeanor, and a focus on the facts.
Choosing the Right Time and Place
The confrontation needs to be in a private, neutral setting where there’s ample time for discussion and no external distractions. I realized that a rushed, public confrontation would be counterproductive.
Creating a Safe Space for Dialogue
The goal is to open a dialogue, not to win an argument. Creating an environment where the individual feels they can speak without immediate judgment is essential.
Presenting Evidence Calmly and Clearly
When presenting the gathered evidence, it’s important to do so in a clear, concise, and non-accusatory manner. The focus should be on the observed behaviors and financial transactions, rather than making sweeping judgments.
Sticking to Observable Facts
I learned to present what I saw and what I found, avoiding emotional language or personal attacks. “I noticed these transactions” is more effective than “You are being scammed and you’re an idiot for letting this happen.”
Listening and Allowing for Explanation
It’s crucial to give the family member an opportunity to explain their actions or beliefs. While the evidence might be compelling, understanding their perspective, even if flawed, is part of the process.
Understanding Their Narrative
Even if their explanation seems implausible, listening empathetically can reveal deeper issues or motivations.
Dealing with Denial and Defensiveness
Denial and defensiveness are common reactions when someone is confronted with such sensitive issues, especially if they are being manipulated or are ashamed.
Recognizing the Psychological Impact of Deception
Individuals who are victims of fraud, especially romance scams, can become deeply invested in the fantasy created by the scammer. This can lead to a fierce defense of the relationship.
The Power of Cognitive Dissonance
When confronted, the brain might try to reconcile the conflicting ideas of believing they are in a genuine relationship and being told it’s a scam. This can lead to strong denial.
Patience and Persistence
Breaking through denial often requires patience and repeated, calm conversations. It’s not a one-time event. I realized that progress might be slow.
Reinforcing Concerns Without Aggression
Gently reiterating concerns and presenting additional evidence as it becomes available can, over time, chip away at defensiveness.
The Role of Professional Support
In such deeply emotional situations, professional intervention can be invaluable.
Seeking Counseling or Therapy
A therapist can help the individual process the trauma of being defrauded, rebuild their self-esteem, and develop healthier coping mechanisms. It also helped me to process my own emotions.
Addressing the Emotional Scars
The psychological impact of fraud can be profound, and therapy provides a safe space to work through these issues.
Involving Other Trusted Family Members or Friends
If appropriate, involving other stable and trusted individuals can provide a support system and a united front. However, this needs to be done with extreme care to avoid further alienating the individual.
A United Front, Not a Gang-Up
The goal is to offer support and guidance, not to ganging up. Careful selection of these individuals is critical.
Legal and Ethical Considerations: Boundaries and Protection

As I delved into this, I quickly realized there were lines I couldn’t cross. Privacy is paramount, and actions taken must be legal and ethical.
Understanding Privacy Laws
It’s crucial to be aware of the privacy laws in my jurisdiction, especially concerning recording conversations or accessing private digital accounts. I never wanted to be on the wrong side of the law myself.
Consent and Recording
In most places, recording a conversation without the consent of all parties involved is illegal. This is a significant hurdle when trying to gather direct evidence of webcam interactions.
When is Consent Required?
Understanding when consent is legally required for recording conversations is non-negotiable. I consulted with legal professionals on this.
Accessing Digital Accounts
Accessing someone’s private digital accounts without their explicit permission is a serious legal offense. I had to respect boundaries.
Respecting Personal Digital Space
Even with suspicions, infringing on someone’s digital privacy can have severe legal repercussions.
When to Report to Authorities
In cases of serious fraud, especially involving exploitation or significant financial loss, reporting to law enforcement or relevant agencies might be necessary.
Child Exploitation and Online Safety
If there’s any suspicion of child exploitation or endangerment, immediate reporting to child protective services or law enforcement is absolutely critical. This overshadows all other concerns.
Prioritizing Safety Above All Else
The safety and well-being of any potential victims, especially children, must be the absolute priority.
Reporting Financial Fraud
For significant financial losses, reporting to consumer protection agencies or law enforcement can help prevent the fraudster from targeting others.
Stopping the Scammer’s Operations
Reporting can contribute to investigations that could lead to the apprehension of the perpetrator and the disruption of their fraudulent activities.
Establishing Boundaries and Seeking Legal Advice
Setting clear boundaries is essential, both for the individual who is being defrauded and for other family members. Seeking legal advice can provide clarity on rights and options.
Defining Clear Lines of Communication and Financial Support
Establishing clear expectations about financial assistance and communication channels can help mitigate future exploitation.
Creating a Safety Net
Defining what the family is willing to offer in terms of support, and what is beyond their capacity, is vital for everyone’s protection.
Consulting with an Attorney
An attorney specializing in fraud or elder law can offer guidance on the legal ramifications of the situation and any available legal remedies.
Proactive Legal Planning
Having legal counsel can help navigate complex situations and ensure that all actions are legally sound.
If you suspect that a family member has used a budget webcam for fraudulent activities, gathering evidence can be crucial in proving your case. One effective approach is to analyze the video quality and features of the webcam in question, as this can help establish whether it was capable of producing the content in question. For more insights on how to approach this situation, you might find it helpful to read a related article that discusses various aspects of digital fraud and the tools used, which you can find here. Understanding the technology involved can aid you in building a stronger argument.
Moving Forward: Rebuilding Trust and Preventing Future Incidents
| Metrics | Data |
|---|---|
| Webcam Brand | Logitech C270 |
| IP Address | 192.168.1.10 |
| Timestamp of Fraudulent Activity | 2022-05-15 10:30:00 |
| Recorded Video Evidence | Yes |
| Location of Fraudulent Activity | Home Office |
Once the situation is addressed and proof is established, the focus shifts to recovery and prevention. This is a long road, and it requires ongoing effort.
Supporting the Victim’s Recovery
The emotional and psychological toll of fraud can be significant. The priority is to support the victim in their healing process.
Encouraging Open Communication About Feelings
Creating a safe space for the victim to express their emotions, fears, and anger is crucial for their recovery.
Acknowledging the Trauma
It’s important to acknowledge that being a victim of fraud is a traumatic experience, and the healing process takes time.
Rebuilding Self-Esteem and Confidence
Fraudsters often target individuals’ vulnerabilities to erode their self-esteem. Rebuilding confidence is a key part of recovery.
Empowering the Individual
Helping the victim regain a sense of control and agency is vital for their long-term well-being.
Educating About Online Safety
Prevention is paramount. Educating family members about online risks and how to identify scams is essential.
Recognizing and Reporting Scams
Teaching family members to be vigilant about suspicious online interactions and to know how to report potential scams is critical.
Creating a Culture of Awareness
Fostering open conversations about online safety within the family can create a more informed and protected environment.
Setting Online Boundaries Together
Working together to establish healthy boundaries for online activity, including sharing personal information and financial practices, can be beneficial.
Collaborative Safety Strategies
Involving all family members in discussions about online safety can promote a shared responsibility for protection.
Rebuilding Family Bonds After Betrayal
The damage to family bonds can be profound. Rebuilding trust requires time, transparency, and consistent effort from all sides.
Open and Honest Dialogue
Maintaining open and honest communication about feelings, concerns, and progress is crucial for healing broken trust.
Rebuilding the Foundation of Trust
This involves consistent actions that demonstrate honesty, reliability, and respect for one another.
Setting Realistic Expectations
Healing and rebuilding trust are processes that take time. Setting realistic expectations for recovery can prevent disappointment and frustration.
Patience and Understanding
Recognizing that forgiveness and reconciliation are not immediate processes is important for both the victim and the perpetrator.
This journey is arduous, and there are no easy answers. But with diligence, a commitment to truth, and a focus on both immediate safety and long-term healing, it is possible to navigate the complexities of webcam fraud within the family and emerge, however scarred, with a clearer understanding and a renewed commitment to protection and well-being. It was a journey I never wanted to take, but one that ultimately reinforced the importance of vigilance, the fragility of trust, and the enduring strength of family, even when tested to its limits.
FAQs
1. How can I prove that a family member used a budget webcam for fraud?
To prove that a family member used a budget webcam for fraud, you can gather evidence such as video recordings, screenshots, or any other digital evidence that shows the fraudulent activity taking place using the webcam.
2. What steps should I take if I suspect a family member of using a budget webcam for fraud?
If you suspect a family member of using a budget webcam for fraud, you should gather evidence of the fraudulent activity, report it to the appropriate authorities, and consider seeking legal advice to understand your options.
3. Can a budget webcam be used for fraudulent activities?
Yes, a budget webcam can be used for fraudulent activities such as identity theft, online scams, or other illegal activities that involve using the webcam to deceive or defraud others.
4. What are some common signs that a family member may be using a budget webcam for fraud?
Common signs that a family member may be using a budget webcam for fraud include secretive behavior around their computer or webcam, unexplained financial transactions, or evidence of them engaging in fraudulent activities online.
5. What legal implications are there for proving a family member used a budget webcam for fraud?
Proving that a family member used a budget webcam for fraud can have legal implications, and it’s important to gather evidence and report the fraudulent activity to the appropriate authorities. Depending on the severity of the fraud, legal action may be taken against the family member.