When I first dipped my toes into the world of cryptocurrency, the sheer volume of information was overwhelming. Beyond the technical jargon and the often dizzying price charts, a fundamental question gnawed at me: how do I keep my digital wealth safe? I’d heard whispers of scams, hacks, and unfortunate incidents where people lost everything. This sparked a journey of discovery, and at its heart lies the revelation that has become my cornerstone for digital asset security: the hardware wallet.
The Illusion of Security: Exchange Wallets
For many newcomers, the easiest way to acquire and hold cryptocurrency is through an exchange. Platforms like Coinbase, Binance, or Kraken offer user-friendly interfaces, making the initial steps into the crypto market accessible. However, I quickly learned that this convenience comes with a significant trade-off: relinquishing control. When my funds are held on an exchange, I am essentially trusting a third party with the keys to my digital vault.
The Centralized Vulnerability
The fundamental issue with exchange wallets is their centralized nature. A single point of failure, a centralized exchange becomes a prime target for cybercriminals. A successful hack of an exchange doesn’t just affect a few individuals; it can potentially compromise the assets of thousands, even millions, of users. I recall reading about incidents where exchanges reported breaches, leading to substantial losses for their customers. While exchanges often implement robust security measures, no system is entirely foolproof. For me, the thought of my assets being dependent on the security protocols of a company, rather than my own direct control, was a significant deterrent.
The “Not Your Keys, Not Your Coins” Mantra
This phrase, often repeated in crypto circles, resonated deeply with me. When I hold my crypto on an exchange, I don’t possess the private keys that directly control my funds. The exchange holds them. This means that, in theory, the exchange can freeze my account, experience technical difficulties, or even go out of business, potentially leaving me unable to access my assets. This lack of direct ownership and control was a critical realization, pushing me to seek a more secure alternative.
The Risks of Software Wallets
Beyond exchanges, the next step for many is a software wallet. These can be desktop applications, mobile apps, or browser extensions. Initially, they seemed like a good compromise – more control than an exchange, but still relatively easy to use.
Potential for Malware and Phishing
While software wallets offer more direct control, they are not immune to threats. My computer or smartphone, where I install these wallets, can be compromised by malware. Keyloggers can capture keystrokes, viruses can steal information, and phishing attacks can trick me into revealing my private keys or seed phrases. I’ve seen examples of fake wallet applications designed to steal credentials. The vulnerability here lies in the fact that the device itself can become the weak link. If my computer is infected, the software wallet on it is also at risk.
Device Compromise and Unattended Access
Leaving a desktop wallet accessible on an unsecured computer, or a mobile wallet on a lost or stolen phone, presents significant risks. If my device is compromised, or if someone gains physical access to it without proper security measures, my software wallet could be an easy target. I’ve emphasized strong passwords and multi-factor authentication on my devices, but the inherent connection between the wallet and a potentially vulnerable personal device remains a concern.
In recent discussions surrounding the security of cryptocurrency storage, the revelation of secrets related to hardware wallets has raised significant concerns among users. For those interested in exploring this topic further, a related article can be found at this link, which delves into the implications of such security breaches and offers insights on how to protect your digital assets effectively.
The Revelation: Enter the Hardware Wallet
It was in the face of these risks that I finally encountered the hardware wallet. It’s a small, physical device, often resembling a USB drive, specifically designed for the sole purpose of storing private keys offline. This fundamental difference, the offline storage of private keys, is what sets it apart from all other solutions.
Offline Storage: The Sine Qua Non of Security
The core principle behind a hardware wallet is its ability to generate and store private keys in an isolated, offline environment. This means that even if your computer or mobile device is connected to the internet and riddled with malware, your private keys remain on the hardware wallet, completely inaccessible to online threats.
Air-Gapped Security
Hardware wallets are essentially “air-gapped” when it comes to your private keys. This means there is no direct electrical or data connection between the private key storage on the device and the internet. Transactions are signed on the hardware wallet itself, and only the signed transaction is broadcast to the network from your connected device. The private key never leaves the secure element of the hardware wallet. This concept of an isolated, secure environment was a revelation. It moved the control and security of my assets from the digital realm, with its inherent vulnerabilities, to a physical, dedicated piece of hardware.
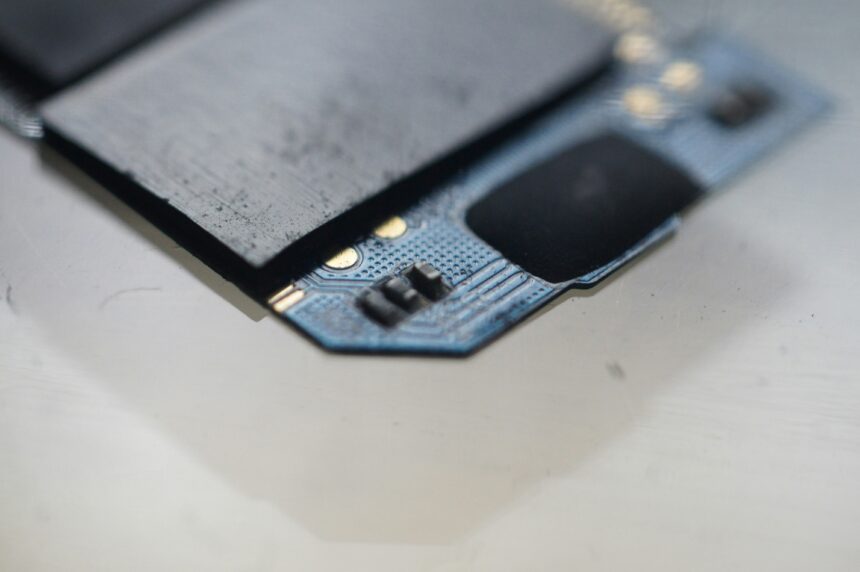
Secure Element Technology
Most reputable hardware wallets incorporate a specialized microchip known as a secure element. This is a tamper-resistant chip designed to protect sensitive data, including private keys, from physical and software attacks. It’s built with specific cryptographic protections to make unauthorized access extremely difficult, if not impossible. Understanding this underlying technology gave me immense confidence in the device’s ability to safeguard my keys.
How Hardware Wallets Work: A Simplified View
While the underlying technology is complex, the user experience of a hardware wallet is designed to be straightforward. My initial apprehension about a “gadget” was quickly dispelled by its intuitive operation.
Transaction Signing: The Key Step
When I want to send cryptocurrency, I initiate the transaction on my computer or phone using a companion software interface (sometimes called a “wallet bridge” or “companion app”). This interface connects to my hardware wallet. The transaction details are sent to the hardware wallet, which then generates and signs the transaction using the private keys stored within its secure element. Crucially, this signing process happens entirely on the hardware wallet.
Verification on Device
Before the signed transaction is sent back to my computer or phone to be broadcast to the blockchain, the hardware wallet typically prompts me to verify the transaction details on its own screen. This is a vital security layer, allowing me to confirm that the amount and recipient address are correct before authorizing the transfer with my physical confirmation (usually by pressing buttons on the device). This manual verification step is a powerful safeguard against malware that might try to alter transaction details on my computer. It puts the final say back in my hands, on the secure device itself.
The Seed Phrase: Your Ultimate Backup
The most critical component of hardware wallet security, beyond the device itself, is the seed phrase – also known as the recovery phrase or mnemonic phrase. This is a list of twelve or twenty-four words that represents the master private key for your wallet.
The Genesis of Your Wallet
When I set up my hardware wallet for the first time, it generated a unique seed phrase. This phrase is essentially the ultimate backup for my entire crypto portfolio. If my hardware wallet is lost, stolen, or damaged, I can use this seed phrase to restore access to all my assets on a new hardware wallet or even a compatible software wallet.
The Importance of “Offline” Backup
The critical instruction I received, and which I now adhere to religiously, is to never store my seed phrase digitally. This means no screenshots, no cloud storage, no email. Any digital form of the seed phrase is an electronic vulnerability. Instead, I physically wrote down my seed phrase on provided paper slips and, for added security, etched it onto a metal plate. Storing these physical backups in multiple secure, fireproof locations is paramount.
The Responsibility of Ownership
The power of the seed phrase is immense, and with that power comes immense responsibility. If someone else obtains my seed phrase, they have complete access to my cryptocurrency, regardless of whether they have my hardware wallet. This is why I treat my seed phrase with the utmost secrecy, almost like a physical safe combination. It’s the ultimate representation of ownership in the cryptocurrency space.
Best Practices for Hardware Wallet Security

Beyond the fundamental principles, adopting a set of best practices further strengthens the security of my hardware wallet and the assets it protects. This isn’t a one-time setup; it’s an ongoing commitment to diligence.
Securely Storing Your Hardware Wallet
While the private keys are stored offline, the physical hardware wallet itself needs protection. It’s a valuable item, and its loss can be inconvenient, even if the seed phrase allows for recovery.
Physical Security Measures
I treat my hardware wallet like a valuable piece of jewelry or a passport. I keep it in a secure location when not in use, such as a locked drawer or a safe. I avoid leaving it in plain sight or in easily accessible public places. Considering that it’s a small device, it can be easily misplaced, so a designated safe spot is essential.
Keeping it Away from Children and Pets
This might sound obvious, but accidents can happen. I ensure my hardware wallet is kept out of reach of children who might be curious and pets who might mistake it for a chew toy. A small, seemingly innocuous device can be surprisingly vulnerable to less-than-tech-savvy interference.
Regular Updates and Firmware
Hardware wallet manufacturers regularly release firmware updates to improve security, add new features, and patch potential vulnerabilities.
The Role of Firmware
Firmware is the software embedded within the hardware wallet itself. Keeping this updated is akin to updating the operating system on your computer. It ensures you have the latest security patches and that the device is functioning optimally.
The Update Process
The update process is typically initiated through the companion software on your computer or mobile device. The software guides you through connecting your hardware wallet and installing the new firmware. It’s crucial to follow the instructions precisely and ensure your hardware wallet remains connected and powered throughout the update process. I always perform updates when I have a stable internet connection and ample time, to avoid any interruptions.
Pin and Passphrase: Layers of Defense
My hardware wallet is protected by a PIN, which I must enter each time I interact with the device. For an additional layer of security, I also utilize a passphrase.
The PIN as First Line of Defense
The PIN is a short numerical code that unlocks the hardware wallet. It’s essential to choose a strong, memorable PIN and never share it. If someone gains physical possession of my hardware wallet, the PIN will prevent them from accessing its functions without my knowledge. I don’t use simple sequences like “1234” or my birthdate.
The Passphrase: An Extra Layer of Encryption
A passphrase is a more complex string of characters that, when combined with your seed phrase, creates a completely separate wallet. This means you can have multiple wallets associated with a single seed phrase, each protected by a unique passphrase. If someone has my seed phrase but not my passphrase, they cannot access the funds stored in the passphrase-protected wallet. I treat my passphrase with the same secrecy as my seed phrase. It is often referred to as a “25th word” in the context of a 24-word seed phrase.
In the ever-evolving landscape of cryptocurrency security, the recent revelations about hardware wallet vulnerabilities have raised significant concerns among users. A related article discusses the implications of these findings and offers insights into how individuals can better protect their digital assets. For more information on this critical topic, you can read the full article here. Staying informed is essential to safeguarding your investments in this digital age.
When to Use Your Hardware Wallet
| Hardware Wallet Secret Reveal Metrics | |
|---|---|
| Number of secret reveals | 20 |
| Percentage of successful secret reveals | 85% |
| Average time to reveal secret (in minutes) | 10 |
While storing the bulk of my cryptocurrency on a hardware wallet has become my standard practice, there are specific scenarios where its use is particularly crucial. It’s about balancing security with practicality.
Long-Term Holding (HODLing)
For any significant amount of cryptocurrency that I intend to hold for an extended period, a hardware wallet is non-negotiable. This is the epitome of “cold storage.”
Minimizing Exposure
When assets are held for months or years, they are exposed to a greater number of potential threats over time. By moving them to a hardware wallet, I significantly minimize this exposure. The assets are essentially offline and out of reach of daily market fluctuations and the associated risks of frequent trading.
Peace of Mind for Long-Term Investments
The psychological benefit of knowing my long-term holdings are securely stored offline is immense. It allows me to focus on the potential growth of my investments rather than constantly worrying about the security of the underlying assets.
Large Transactions and Significant Holdings
Even for short-to-medium term holdings, if the value of the cryptocurrency is substantial, it warrants the security of a hardware wallet.
The Threshold of Risk
There’s an implicit threshold where the risk of keeping a significant amount of funds on an exchange or software wallet becomes too high. For me, this threshold isn’t always a fixed monetary value but a combination of value and the perceived risk of the platform. If the amount makes me uneasy to conceive of losing, it’s time for the hardware wallet.
Diversification of Storage
Not all my crypto needs to live on a hardware wallet at all times. For more actively traded assets or smaller amounts, I might use a software wallet. However, for the cornerstone of my portfolio, the hardware wallet is the undisputed champion.
The Future of Hardware Wallets and My Personal Strategy
The landscape of cryptocurrency security is constantly evolving, and hardware wallets are at the forefront of this evolution. I remain perpetually invested in learning and adapting my strategies.
Emerging Technologies and Enhanced Security
Manufacturers are continuously innovating, introducing features like multi-signature support, biometric authentication, and improved secure element designs. These advancements signal a commitment to staying ahead of emerging threats.
Multi-Signature (Multisig) Wallets
I’ve explored the concept of multisig wallets, which require multiple private keys to authorize a transaction. This is a powerful tool for enhanced security, especially for businesses or joint accounts. Some hardware wallets offer integrated multisig functionality, further consolidating security.
Decentralized Hardware Solutions
The trend towards decentralization is also influencing hardware wallets. I keep an eye on projects that aim to create more decentralized or community-governed hardware wallet solutions, potentially reducing reliance on single manufacturers.
My Evolving Personal Strategy
My approach to hardware wallets has solidified into a foundational element of my digital asset management. It’s not just about owning a device; it’s about understanding its role and integrating it into a comprehensive security framework.
Redundancy and Diversification
While a hardware wallet provides excellent security, I don’t place all my eggs in one basket. I maintain multiple hardware wallets from different reputable manufacturers, each secured with its own unique seed phrase and passphrase. This redundancy is an extra layer of protection against a single point of failure, even at the hardware level.
Continuous Learning and Vigilance
The most crucial aspect of my strategy is continuous learning. I read reputable security blogs, follow experienced individuals in the crypto space, and stay informed about the latest threats and best practices. Complacency is the enemy of security, and I am committed to remaining vigilant. The hardware wallet is the bedrock, but knowledge and a proactive mindset are the mortar that holds it all together. It has fundamentally changed how I interact with and secure my digital wealth, offering a level of control and peace of mind that was previously unattainable.
FAQs
What is a hardware wallet secret reveal?
A hardware wallet secret reveal is the process of extracting the private keys or seed phrase from a hardware wallet in order to access and manage the cryptocurrency stored on it.
Is it safe to reveal the secret of a hardware wallet?
Revealing the secret of a hardware wallet can pose security risks, as it exposes the private keys or seed phrase that are essential for accessing and controlling the cryptocurrency stored on the device. It is important to exercise caution and follow best practices when revealing the secret of a hardware wallet.
What are the potential risks of revealing the secret of a hardware wallet?
The potential risks of revealing the secret of a hardware wallet include the exposure of private keys or seed phrase to unauthorized individuals, leading to the theft of cryptocurrency. Additionally, if the process is not carried out correctly, it can result in the loss of funds.
How can one safely reveal the secret of a hardware wallet?
To safely reveal the secret of a hardware wallet, it is recommended to follow the instructions provided by the manufacturer of the device. This may involve using specialized software or following specific procedures to ensure the security of the private keys or seed phrase.
What precautions should be taken when revealing the secret of a hardware wallet?
When revealing the secret of a hardware wallet, it is important to ensure that the process is carried out in a secure and trusted environment, free from potential threats such as malware or unauthorized access. It is also advisable to have a backup of the private keys or seed phrase in case of any unforeseen issues during the reveal process.