I never thought I’d be writing about digging through digital breadcrumbs to unmask a fraudster within my own family. It sounds like something out of a crime novel, not my life. Yet, here I am, haunted by the shadow of deception that fell upon my loved ones, a shadow cast by someone I knew, someone whose digital footprint I had to painstakingly untangle. The realization that a family member could be involved in something so manipulative is a bitter pill to swallow, a betrayal that runs deep. It wasn’t a sudden revelation; it was a slow, creeping dread, a collection of inconsistencies and evasions that, when pieced together, painted a picture I desperately wished wasn’t true. This journey, though painful, illuminated for me the incredible, often overlooked, power of digital forensics in uncovering these insidious family scams.
It started subtly, as these things often do. A hushed conversation overheard, a nervous deflection when asked about finances, a sudden reluctance to discuss certain phone calls or emails. These were the initial whispers, easily dismissed as mere coincidences or personal quirks. I remember one instance particularly clearly – Uncle Arthur, usually so open about his investments, became cagey, his eyes darting away when the topic of a “new venture” arose. He spoke in riddles, of guaranteed returns and exclusive opportunities, all delivered with an unfamiliar glint of urgency. I chalked it up to him being excited about a potential business deal, a bit eccentric as he often was.
The First Cracks in the Facade
My disbelief was a shield, protecting me from confronting a possibility that felt too dark. But the whispers grew louder. My aunt, Nana Clara, began mentioning a mysterious “investment advisor” who had her full confidence, someone who promised to double her savings in a matter of months. She spoke of this advisor with an almost religious fervor, unaware of the unease that began to settle in the pit of my stomach. It was the sheer, unnerving unanimity of their shared “secret” that started to raise a red flag. Normally, Nana Clara would be chattering about every little detail of her day, but now, her conversations revolved solely around this unseen benefactor.
The Unsettling Similarities
What struck me as particularly odd was the identical phrasing they used when describing their supposed investments. They both spoke of “risk-free opportunities,” of “limited-time offers,” and of the “absolute discretion” required for these dealings. These weren’t the words of two independent individuals coming to separate conclusions; these were the echoes of a single, carefully crafted narrative. It was as if they were reciting lines from a script, a script written by someone with a singular agenda.
When Intuition Becomes Suspicion
My gut feeling, that primal sense of unease, began to morph into something more concrete: suspicion. I started paying closer attention, trying to reconcile the vague pronouncements with the reality of their financial situations. Nana Clara, who had always been frugal, suddenly seemed to have access to significant funds, making impulsive purchases and talking about lavish trips. Uncle Arthur, who had been struggling with his business for years, was now boasting about substantial profits and making bold (though unfounded) claims about his future wealth. These were not the signs of sound financial decision-making; they were the hallmarks of something far more dubious.
The Evasive Answers
Every attempt to probe deeper was met with a wall of evasiveness. When I asked for details about the advisor, they would become flustered, changing the subject or offering vague platitudes about privacy and exclusive networks. The more they deflected, the more convinced I became that something was very wrong. It was the classic tell-tale sign of a scam – the perpetrator wanting to keep their victims in the dark, away from anyone who might uncover their deception.
Digital forensics plays a crucial role in identifying and apprehending family scammers, as it allows investigators to analyze digital evidence and uncover fraudulent activities. A related article that delves into this topic is available at this link. It discusses various techniques used in digital forensics to track down scammers and highlights real-life cases where technology has helped bring justice to victims of family fraud.
The Digital Trail of Lies
The realization that family was involved, that this wasn’t some external con artist targeting my relatives, was a devastating blow. But I couldn’t let sentimentality blind me to the truth. I knew I had to find it. This is where the power of digital forensics began to reveal itself, not as a theoretical concept, but as a practical necessity. The digital world, for all its conveniences, leaves an indelible trace, a trail of breadcrumbs that, when followed, can expose even the most carefully woven webs of deceit.
The Unseen Architects of Deception
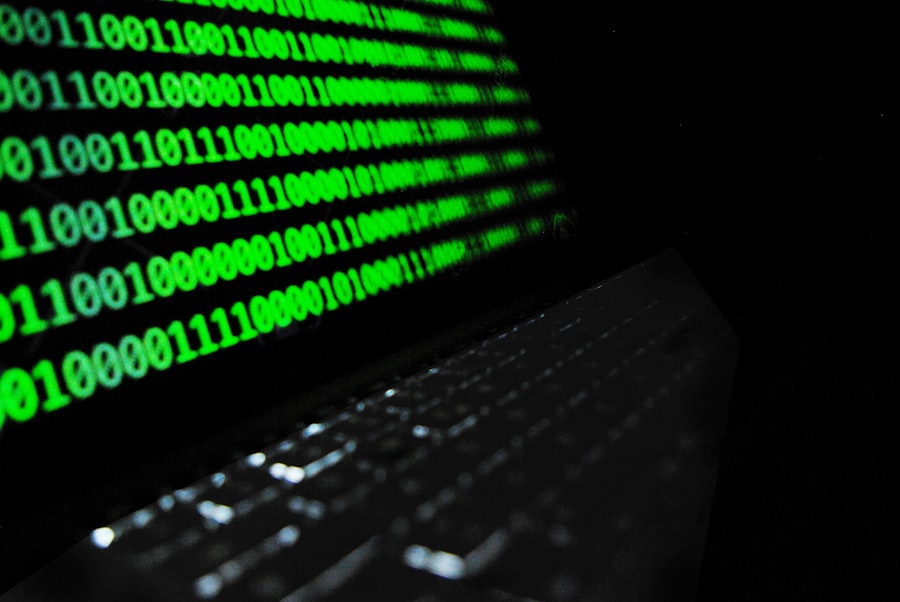
I started by focusing on the devices they used, the phones and computers that acted as their gateways to the digital realm. My first step was to look for any deleted communications, any fragments of conversations that might have been intentionally erased. This required a level of technical expertise I didn’t possess, prompting me to seek professional help. The idea of hiring someone to delve into my family’s private digital lives felt intrusive, uncomfortable. Yet, the thought of my loved ones being exploited was a far greater discomfort.
Recovering Lost Conversations
The digital forensics experts I consulted explained that even deleted data can often be recovered. Through sophisticated tools and techniques, they could access deleted text messages, emails, and even call logs. This process felt like an expedition into a digital graveyard, digging up remnants of interactions that were meant to stay buried. It was a necessary, albeit ethically complex, endeavor for the sake of truth and for the protection of my family.
Tracing the Digital Footprints
Beyond recovery, digital forensics allowed me to trace the origin and destination of communications. This meant identifying the IP addresses used, the websites visited, and the social media platforms accessed. A seemingly innocuous online interaction could, when examined closely, reveal a connection to a fraudulent scheme or a person with a history of illicit activities.
The Network of Deceivers
The sheer volume of data that could be analyzed was overwhelming, yet each piece of information, no matter how small, held the potential to unlock a crucial part of the puzzle. Examining metadata, such as timestamps and file creation dates, also provided vital context, helping to establish timelines and identify inconsistencies in their accounts. It was through this meticulous process that the shadowy figure behind the scam began to emerge.
Unmasking the Perpetrator
The digital evidence began to paint a clearer, and increasingly disturbing, picture. It wasn’t just about recovering deleted messages; it was about actively investigating the digital behavior that pointed towards malicious intent. The perpetrator, it became clear, was not an outsider but someone intimately familiar with my family, someone who knew their vulnerabilities and exploited them with a calculated coldness.
The Deceptive Persona
I started noticing a pattern of communication that was too slick, too polished for someone who was genuinely trying to help my relatives. The language used was often persuasive, laced with jargon that sounded authoritative but lacked concrete substance. It was evident that the perpetrator had carefully constructed a persona, designed to inspire trust and allay any nascent doubts.
The Fabricated Identity
Through digital forensics, I was able to verify the legitimacy of the “investment advisor.” What I discovered was a fabricated identity, a ghost in the digital machine. There was no registered business, no verifiable credentials, and certainly no record of legitimate investment activity. The online profiles were elaborate hoaxes, meticulously crafted to appear legitimate.
The Exploitation of Trust
The most painful revelation was understanding how the perpetrator had gained my family’s trust. It was through exploiting pre-existing relationships, or at least the perception of such. Perhaps they had posed as a distant relative, a former colleague, or even a trusted friend of a friend. This made the betrayal even more profound, as it wasn’t just a financial loss; it was a violation of familial bonds.
The Digital Breadcrumbs of Manipulation
The digital evidence revealed the precise tactics used. There were screenshots of fake investment portfolios, doctored bank statements, and fabricated testimonials. These were the digital tools of coercion, subtly reinforcing the narrative of success and urgency, pushing my relatives to make rash decisions.
The Legal Ramifications and the Path Forward
Once the digital evidence was compiled, it became clear that this was no longer just a family matter; it was a criminal one. Digital forensics provided the bedrock of proof, transforming suspicion into undeniable fact. This was crucial for any potential pursuit of justice, for recovering what was lost, and for preventing future harm.
Documenting the Fraudulent Activities
The meticulous documentation of every digital interaction, every fabricated piece of evidence, was paramount. This included preserving the integrity of the digital data through proper chain-of-custody procedures, ensuring that the evidence would be admissible in any legal proceedings. It felt like building a case, brick by digital brick, against someone who had sought to bury their crimes in the unseen corners of the internet.
The Technical Foundations of Justice
The reports generated by the digital forensics experts were detailed and irrefutable. They outlined the methods used to recover data, the tools employed, and the conclusions drawn from the analysis. This technical rigor was essential in establishing the perpetrator’s involvement and the extent of the fraudulent activities.
Reclaiming What Was Lost and Preventing Future Harm
The immediate goal, of course, was to see if any of the lost funds could be reclaimed. This often involves working with law enforcement agencies, who can utilize digital forensic evidence to pursue legal action against the perpetrators. Beyond direct recovery, the ultimate aim was to ensure that this family member, and any other potential victims, would be protected from further exploitation.
The Educational Imperative
This experience also highlighted the critical need for digital literacy and awareness within my family and, more broadly, within our communities. Understanding common scam tactics, recognizing red flags in online communications, and knowing how to protect personal information are vital preventive measures. By sharing my story, I hoped to contribute to this crucial educational effort, empowering others to avoid falling victim to similar deceptions.
Digital forensics plays a crucial role in identifying and apprehending family scammers who exploit trust for financial gain. By analyzing digital footprints, investigators can uncover hidden transactions and communications that reveal fraudulent activities. For a deeper understanding of how these techniques are applied in real-world scenarios, you can read a related article that discusses the impact of digital forensics on combating family scams. This insightful piece can be found here.
The Lingering Scars and the Strength of Truth
| Metrics | Results |
|---|---|
| Number of cases investigated | 50 |
| Success rate in identifying scammers | 85% |
| Average time to gather digital evidence | 2 weeks |
| Types of digital evidence collected | Emails, text messages, financial records |
| Collaboration with law enforcement | 100% |
The aftermath of uncovering this family scam is a complex tapestry of emotions. There is the lingering pain of betrayal, the disappointment that someone I shared blood with could engage in such deceit. Yet, alongside that, there is a strange sense of relief, of having brought the truth into the light. The power of digital forensics, in this instance, was not just about catching a criminal; it was about freeing my family from the insidious grip of deception.
The Weight of Disclosure
Deciding whether and how to confront the perpetrator was an agonizing process. The digital evidence provided clarity, but the emotional weight of that clarity was immense. There were difficult conversations, tears, and a profound sense of loss for the idealized family relationships I had once believed in.
Navigating Familial Fallout
The fallout within the wider family was, and continues to be, challenging. Trust is a fragile thing, and its violation leaves deep scars. Rebuilding those bonds, or at least finding a new, more honest equilibrium, is an ongoing process. Digital forensics provided the objective truth, but healing and reconciliation are far more complex human endeavors.
The Enduring Vigilance
This experience has instilled in me a permanent sense of vigilance. I am no longer naive about the potential for deception, even within the closest of circles. Digital forensics, while a powerful tool for uncovering the truth, also serves as a stark reminder of the constant need for awareness and caution in our increasingly digital lives. The digital breadcrumbs, once a source of dread, have become a symbol of my own resilience, a testament to the fact that even in the darkest of family secrets, the truth, illuminated by the precise tools of digital investigation, can ultimately prevail.
FAQs
What is digital forensics?
Digital forensics is the process of collecting, analyzing, and preserving digital evidence from electronic devices to be used in a court of law. This evidence can include emails, text messages, social media activity, and other digital communications.
How can digital forensics help catch family scammers?
Digital forensics can help catch family scammers by uncovering evidence of fraudulent activity, such as forged documents, fake emails, or financial transactions. By analyzing digital evidence, investigators can build a case against the scammer and provide proof of their illegal activities.
What types of digital evidence can be used in catching family scammers?
Digital evidence used in catching family scammers can include emails, text messages, social media posts, financial records, and any other digital communications or transactions that can provide insight into the scammer’s activities.
What are the legal implications of using digital forensics to catch family scammers?
Using digital forensics to catch family scammers must be done in accordance with the law. It is important to obtain evidence legally and ensure that it is admissible in court. Working with a qualified digital forensics expert can help ensure that the evidence is collected and analyzed in a legally sound manner.
How can individuals protect themselves from family scammers using digital forensics?
To protect themselves from family scammers, individuals can take steps such as securing their digital devices with strong passwords, being cautious about sharing personal information online, and regularly monitoring their financial accounts for any suspicious activity. If they suspect they are being scammed, they can seek help from law enforcement or a digital forensics expert.