How to Prove Webcam Model Mismatch in Legal Video
When I first encountered the challenge of proving webcam model mismatch in legal video, it felt like navigating a labyrinth. The stakes were incredibly high, and the nuances of digital…
Secure Digital Log Notarization with Trusted Time Authority
I've been wrestling with the concept of securing digital logs for a while now. As someone who relies heavily on accurate and verifiable records, whether for personal projects, professional endeavors,…
Implementing Webhooks for Instant Fraud Alerts
I’ve always been fascinated by systems that operate in near real-time, especially when those systems are designed to protect against something as dynamic and potentially damaging as fraud. For a…
Family’s Fake Heart Attack Ends in Satisfying Karma
The frantic call from my sister, Sarah, was enough to send a jolt of adrenaline through me. Her voice, strained and breathless, painted a picture of imminent crisis: Mom, down…
Detecting Faked Signature Pressure: Proven Methods
Detecting Faked Signature Pressure: Proven Methods As someone who has spent considerable time scrutinizing documents, I've learned that the seemingly simple act of signing a name can hold a wealth…
Protecting Privacy: Faraday Box for Forensic Logger
I'm a digital forensics investigator, and while the tools I use are designed to retrieve and analyze data, I've become increasingly aware of a critical, often overlooked aspect of my…
Securing Inheritance Accounts with Hardware Keys
I’ve always been a bit of a worrier, especially when it comes to things that feel fundamentally important, like protecting my financial future and, by extension, the future of my…
The Testimony of a Beloved Home: A Satisfying Probate Court Story
The dust motes danced in the shafts of sunlight slanting through the living room window, a familiar, comforting sight. This house, this unchanging nucleus of my childhood memories, was about…
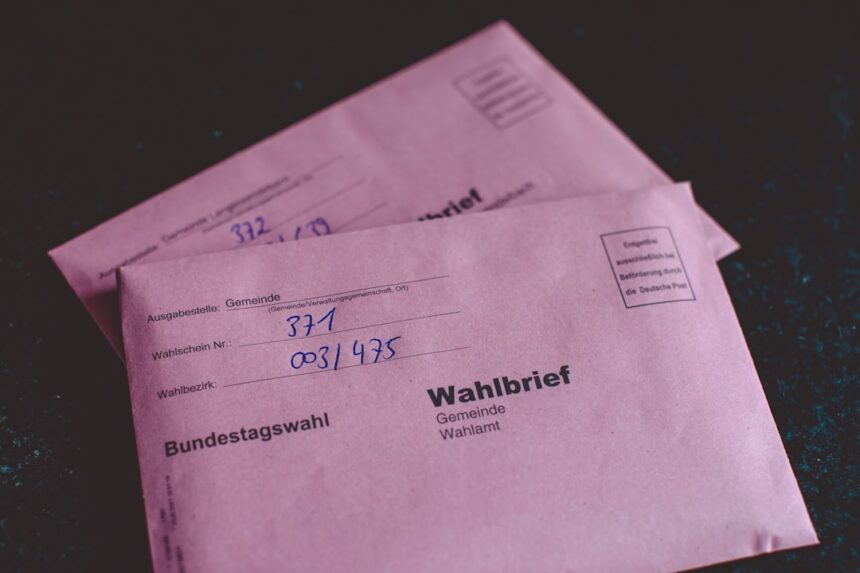
Proving Laser Printer Document Origin
I've often wondered about the genesis of documents, especially in a professional setting where authenticity and origin can be critical. The digital age has brought a certain fluidity to document…
Identifying Spoofed Calls with SIP Headers
I've always found the persistent nuisance of spoofed calls to be particularly irritating. It's not just the unsolicited interruptions; it’s the deliberate deception that grates on me. I’ve dabbled in…