I’ve always considered myself a fairly observant person. Not in a way that makes people uncomfortable, I don’t think. More like I notice the little things, the subtle shifts in an environment, the nuances in a conversation. It’s a habit, I suppose, cultivated over years of quiet introspection and a natural inclination towards analysis. This particular trait, however, found itself tested, and then thoroughly confirmed, by an episode involving my older brother, Daniel.
The Unfolding Mystery
It started subtly, as these things often do. A shift in Daniel’s routine. He’d always been a creature of habit, a predictable presence in the household. Our shared evenings were usually marked by similar activities: him hunched over his laptop, me engrossed in a book, or the occasional shared meal where conversations flowed easily, a comfortable rhythm established over decades of siblinghood. But then, the late nights began. Not just occasionally, but consistently. When I’d ask him about it, I’d get vague answers. “Just catching up on some work,” or “Got a lot on my mind, you know?” Standard evasion, the kind I’d learned to recognize.
Subtle Changes
He’d also started being more secretive. Not overtly, but subtly. His laptop, which was usually an open book – metaphorically speaking, of course, I have no interest in reading his emails – was now often closed when I entered the room. He’d quickly minimize windows, or worse, would be using a different device altogether, one I hadn’t seen him use before. This was unusual for Daniel, who was generally transparent about his technological life. He’d always been the one to troubleshoot my computer issues, to explain new software. For him to suddenly become guarded felt…off.
The Whispers of Suspicion
My suspicions, initially a faint murmur in the back of my mind, began to grow louder. It wasn’t a malicious suspicion, by any means. It was more a sense of unease, a feeling that something significant was happening that I was being excluded from. Daniel and I have always been close, albeit in our own quiet ways. We’ve navigated childhood arguments, teenage angst, and the general awkwardness of early adulthood side-by-side. To feel this sudden chasm opening between us, without any explanation, was unsettling. I started to pay more attention, to catalogue the small anomalies. The hushed phone calls he’d take in his room, closing the door behind him. The way he’d sometimes jump when I entered a room unexpectedly. These were not the actions of someone simply engrossed in work.
As the days turned into weeks, the pattern solidified. Daniel was engaging in a behavior that was demonstrably different from his usual, predictable self. The late nights weren’t just about work; they were about something that occupied his attention so intensely that it encroached on his sleep and altered his social interactions within the home.
Altered Schedules and Social Withdrawals
His sleep schedule was the most obvious indicator. He’d previously been a morning person, up and about, making coffee. Now, he was often barely awake when I left for my own day, and then he’d be up long after I’d retired. This wasn’t a temporary phase; it was becoming a new normal. Furthermore, his participation in shared activities dwindled. Movie nights became rare; shared conversations were shorter, more superficial. When I attempted to initiate deeper discussions about his day or his thoughts, I was met with polite but firm deflection. It felt as though he was actively withdrawing, building a wall around himself.
The Silent Conversations
I observed his phone usage with a growing sense of curiosity mixed with concern. He’d spend an inordinate amount of time on his phone, his thumb scrolling rapidly, his expression often unreadable. Sometimes, a faint smile would flicker across his face, only to be replaced by a furrowed brow. These were not the typical exchanges of texts with friends. The duration and intensity suggested something more consuming. I heard snippets of conversations, but they were always too quiet, too rushed, for me to discern anything of substance. It was like trying to catch a whisper in a strong wind.
The Unexplained Absences
There were also periods where he would simply disappear for several hours without a word. He wouldn’t say he was going out, wouldn’t give a destination or an estimated return time. He’d just be gone, and then reappear as if he’d never left, a casual explanation of errands or a brief walk offered as if it were the most natural thing in the world. While our family has always valued individual freedom and space, Daniel’s previous communication about his movements had been more consistent. This sudden, unannounced absence felt like another brick in the wall he was building.
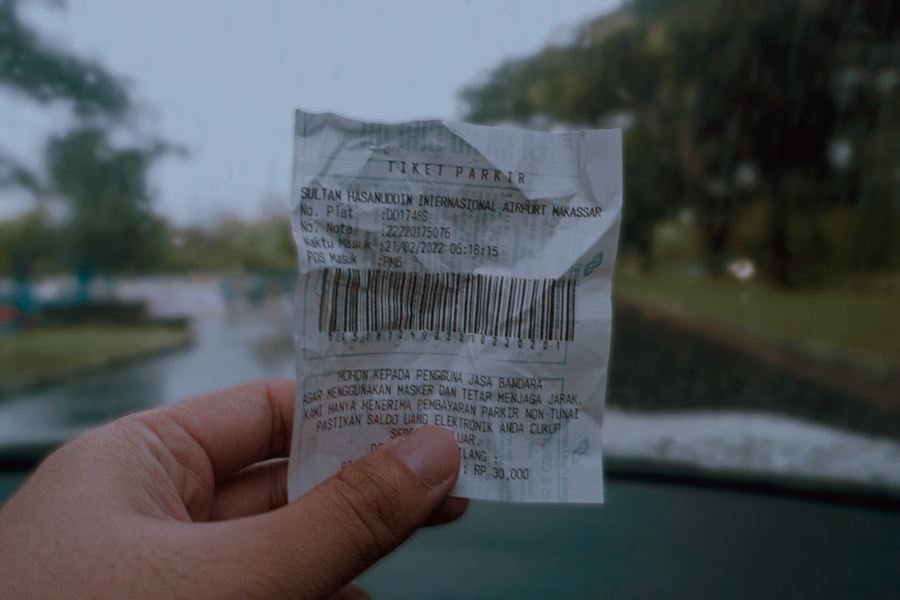
In a recent article titled “Caught in the Act: How Metadata Receipts Expose Hidden Truths,” the implications of metadata in digital transactions are explored in depth. The piece highlights a case where a brother was inadvertently implicated in a scheme due to the detailed information contained within metadata receipts. This incident underscores the importance of understanding how metadata can reveal more than one might expect. For more insights on this topic, you can read the full article here: Caught in the Act: How Metadata Receipts Expose Hidden Truths.
The First Glimmer of Revelation
The actual moment of realization didn’t come with a dramatic confrontation or a sudden confession. It was far more mundane, almost anticlimactic. It happened one evening, when I was looking for a charger for my portable speaker. My search led me to Daniel’s room, which I rarely entered unless invited.
In a recent investigation into the use of metadata receipts, a fascinating article revealed how digital footprints can sometimes catch individuals in the act, leading to unexpected consequences. This intriguing piece highlights the importance of being aware of the data we generate and how it can be traced back to us. To explore this topic further, you can read the full article on the implications of metadata by following this link.
A Displaced Item
I rummaged through his desk drawers, a bit hesitantly at first, but desperation for my speaker trumped my usual respect for his privacy. It was in a drawer I’d assumed would be filled with old cables and forgotten stationery that I found it. It wasn’t the charger I was looking for. It was a small, sleek, black device, completely unfamiliar to me. It was slightly warm to the touch, suggesting recent use.
The Intriguing Device
Curiosity, which had been simmering for weeks, now came to a rolling boil. I picked it up. It was heavier than it looked, with a small, almost invisible screen. There were no obvious buttons, and it seemed to have an almost futuristic design. I’d never seen anything like it connected to Daniel’s usual tech arsenal. He was a smart guy, technically proficient, but his preferences usually leaned towards established brands and familiar interfaces. This was something different.
A Moment of Hesitation
My first instinct was to put it back, to pretend I hadn’t seen it. But the mystery it represented was too compelling. The weeks of speculation, the subtle evasions, the hushed phone calls – it all seemed to point to this unknown object, this anomaly in Daniel’s carefully curated world. I knew I was crossing a line, but the need to understand was overwhelming. I hesitated for a moment, wrestling with my conscience, before a stronger urge to uncover the truth took over.
The Unveiling of the Secret
The device in my hand was the key. It wasn’t just a piece of technology; it was a gateway to understanding Daniel’s hidden life. It took me a while to figure out how to operate it, to unlock its secrets.
Accessing the Contents
I turned it over and over, searching for a power button or a charging port. Eventually, I discovered a subtle pressure point on the side that, when pressed, caused the screen to glow to life. The interface was minimalist and intuitive. It looked like a specialized piece of hardware, designed for a specific purpose. I braced myself, expecting to find anything from illicit online activity to some bizarre hobby. What I found was far more specific, and in its own way, more profound.
Digital Footprints and Hidden Worlds
The device was essentially a portable gambling terminal. Not the kind you’d find in a casino, but a highly sophisticated, internet-connected device that facilitated online betting. The screen displayed a dizzying array of options: virtual slot machines, simulated card games, and what appeared to be live sports betting platforms. There were records of transactions, deposits, and withdrawals, all meticulously logged. The dates and times corresponded with Daniel’s late nights and unexplained absences.
The Unforeseen Extent
The sheer volume of activity was staggering. It wasn’t just a casual flutter; it was deep, consistent engagement. I scrolled through the transaction history, my initial apprehension gradually morphing into a more serious concern. The stakes were higher than I could have imagined. The numbers associated with some of the bets were significant, far beyond what I believed Daniel’s disposable income could comfortably sustain.
The Stark Reality and My Own Reaction

Seeing the evidence laid out so starkly was a difficult experience. It wasn’t just about discovering a secret; it was about confronting a reality that was far more complex and potentially damaging than I had anticipated.
Confronting the Implications
The initial shock gave way to a wave of conflicting emotions. There was disappointment, certainly, that Daniel had felt the need to hide this from me, from our family. But beneath that, a more profound worry began to surface. Online gambling, especially at the level suggested by the device’s activity, carried significant risks. The potential for financial ruin, for addiction, for the erosion of his well-being, were all immediate concerns. I realized that my observer role had now transitioned into something much more serious.
The Weight of Knowledge
I sat there for a long time, the device still in my hands, the glow of its screen illuminating the quiet room. The implications of my discovery pressed down on me. Daniel, my brother, the person I thought I knew so intimately, had been living a double life, a secret existence that was financially risky and emotionally isolating. The feeling of being excluded was still there, but it was now overshadowed by a deep-seated concern for his welfare. The ease with which I had uncovered this secret felt almost like a betrayal, not of Daniel, but of the trust that should exist between siblings.
The Path Forward
The question then became: what do I do now? Do I confront him immediately? Do I try to gather more information? Do I seek professional advice? The weight of this knowledge felt immense, and I knew that my next steps would have a significant impact, not just on Daniel, but on our relationship and the entire family dynamic. The detective work was over, but the real challenge, the challenge of addressing the problem, was just beginning.
FAQs
What are metadata receipts?
Metadata receipts are records of the metadata associated with a particular file or communication. This can include information such as the date and time the file was created, modified, or accessed, as well as details about the device or software used to create or modify the file.
How can metadata receipts be used to catch someone in the act?
Metadata receipts can be used to provide evidence of when and how a file was accessed or modified. For example, in the case of the article, a brother was caught in the act of accessing a file by the metadata receipts associated with the file, which showed the date, time, and device used to access it.
What are some common types of metadata found in receipts?
Common types of metadata found in receipts include file creation and modification dates, author information, file size, and details about the software and devices used to create or modify the file.
How can individuals protect themselves from being caught by metadata receipts?
To protect themselves from being caught by metadata receipts, individuals can take steps such as removing or modifying metadata before sharing files, using secure and private communication methods, and being mindful of the information they share and access online.
Are metadata receipts legally admissible as evidence in court?
Metadata receipts can be legally admissible as evidence in court, but their admissibility and weight as evidence may vary depending on the specific circumstances and the jurisdiction in which the case is being heard. It is important to consult with legal professionals for specific guidance on the use of metadata receipts as evidence.




