I’ve always considered myself a fairly cautious person. I meticulously manage my finances, lock my doors, and generally try to anticipate potential problems before they manifest. So, when I first learned about the concept of device fingerprinting, I was struck by its quiet, almost invisible efficiency. It felt like a digital manifestation of the vigilance I already practiced in the physical world, and the implications for combating a specific kind of financial predator – inheritance thieves – became immediately clear to me.
The notion of someone stealing an inheritance might conjure images of elaborate cons or family feuds. While those scenarios exist, the reality for many is far more insidious. Inheritance theft, in its most common digital form, often involves individuals who exploit the vulnerabilities of grieving beneficiaries or those who are less tech-savvy to gain unauthorized access to financial accounts or sensitive information.
The Grieving Process as a Vulnerability
When someone passes away, their loved ones are thrust into a whirlwind of emotional turmoil and practical necessities. Amidst the grief, the arduous task of settling an estate, accessing bank accounts, and securing assets can feel overwhelming. This heightened emotional state can unfortunately make individuals more susceptible to scams. Scammers, by nature, are adept at identifying and exploiting moments of weakness.
Digital Footprints and Their Unseen Guardians
In the past, securing physical assets was a matter of tangible locks and keys. Today, much of our financial world exists online. This shift has created new avenues for exploitation. Inheritance thieves don’t necessarily need a crowbar to access a digital vault. They might leverage social engineering, phishing attacks, or even exploit weak security protocols to gain access. This is where the concept of device fingerprinting, a seemingly technical detail, becomes a crucial guardian.
In a recent article, the innovative use of device fingerprinting technology has proven instrumental in catching inheritance thieves who attempt to exploit the vulnerabilities of digital estates. This method allows for the identification of unique devices accessing sensitive information, thereby helping law enforcement track down those who illegally claim inheritances. For more insights on this topic, you can read the full article here: Inheritance Thieves Caught Using Device Fingerprinting.
What Exactly is Device Fingerprinting?
At its core, device fingerprinting is a technique used to identify and distinguish a specific computing device from all others. It’s not about identifying the person using the device, but rather the device itself. Think of it as assigning a unique identifier to your smartphone, laptop, or tablet based on a collection of its attributes.
The Anatomy of a Device Fingerprint
This fingerprint is composed of a wide array of data points. These can include:
Hardware Identifiers
- CPU Information: Details about the processor, such as its type and manufacturer.
- Graphics Card Model: The specific graphics processing unit installed.
- Screen Resolution and Color Depth: The display’s capabilities.
- Audio Hardware: Information about the sound card.
- Operating System Version: The specific version of Windows, macOS, iOS, or Android.
Software Configurations
- Installed Fonts: The unique set of fonts available on the device.
- Browser Plugins and Extensions: The software add-ons integrated with the web browser.
- Language Settings: The device’s preferred language and regional settings.
- Time Zone: The configured time zone.
- User Agent String: A string of text sent by the browser that identifies the browser, operating system, and other information.
Network and Connectivity Data
- IP Address: While not always static and can be masked, it’s a significant component.
- MAC Address (sometimes accessible): A unique hardware identifier for network interfaces.
- Wi-Fi Information: Details about connected Wi-Fi networks.
- Bluetooth Information: Data related to Bluetooth capabilities.
The combination of these, and often many more, creates a highly specific signature for each device. It’s highly unlikely that two devices, even of the same model, will have the exact same configuration of these attributes.
The Role of Third-Party Services
Many of the technologies that enable effective device fingerprinting are implemented by third-party services, often integrated into websites and applications. These services analyze the data points I’ve outlined and generate the unique fingerprint. They operate in the background, collecting information without explicit user interaction beyond the act of browsing or using an application.
Distinguishing from Cookies
It’s crucial to understand that device fingerprinting is distinct from browser cookies. While cookies store small pieces of data on a user’s device to remember preferences or track activity within a specific website, device fingerprinting aims to identify the device itself, regardless of cookies (which can be deleted or blocked). This makes it a more persistent and robust identification method.
How Device Fingerprinting Thwarts Inheritance Thieves

The ability of device fingerprinting to identify a specific device is where its power lies in preventing inheritance theft. By recognizing a user’s familiar device, financial institutions and online platforms can establish a baseline of expected activity. When deviations occur, it raises a red flag, potentially stopping a thief in their tracks.
Establishing a Baseline of Trust
When I access my bank account from my usual laptop at my home IP address, the system recognizes my familiar fingerprint. This is a signal of legitimacy. I have a history of accessing my account from this device, and its configuration is consistent with past interactions. This creates an established baseline of trust.
Detecting Anomalous Access Patterns
The real power emerges when someone else tries to access my accounts. If a scammer, having obtained my login credentials through phishing or other means, attempts to log in from a completely unfamiliar device in a different geographic location, the system will immediately notice a discrepancy.
Geographic Inconsistencies
If my account is routinely accessed from my home country, and suddenly a login attempt comes from a device located thousands of miles away, this is a significant deviation. Device fingerprinting can add another layer of verification beyond just the IP address.
Device Signature Mismatch
Even if the thief manages to mask their IP address or uses a VPN, the device fingerprint itself will likely be vastly different from my usual one. A new operating system, a different browser, an unusual set of fonts, or varying hardware identifiers will all contribute to a unique and unfamiliar fingerprint.
Multi-Factor Authentication Enhancement
Device fingerprinting acts as a powerful complement to multi-factor authentication (MFA). MFA, such as sending a code to my phone, requires multiple pieces of evidence to verify my identity.
The Silent Guardian of MFA
When I log in from my usual device, the system might even implicitly trust the MFA prompt more. Conversely, if I log in from an unknown device, the MFA step becomes even more critical, and the system might impose stricter verification protocols. This layered approach significantly increases the difficulty for an unauthorized individual to succeed.
Preventing Account Takeover
Inheritance thieves often aim for account takeover. They want to impersonate the rightful beneficiary and drain funds. By recognizing that the device being used to initiate this takeover is not the legitimate user’s device, the system can block the attempt before any financial damage is done.
The Role of Financial Institutions
Financial institutions are at the forefront of implementing these security measures. They invest heavily in sophisticated fraud detection systems, and device fingerprinting is a cornerstone of these systems.
Proactive Fraud Prevention
Instead of waiting for a fraudulent transaction to occur and then trying to recover lost funds, device fingerprinting enables proactive prevention. It allows the institution to identify potentially malicious activity before it impacts a customer’s account.
Reducing False Positives
While robust security is essential, it’s also important to minimize inconvenience for legitimate users. Device fingerprinting, when implemented effectively, can help reduce false positives. Because the system has a reliable identifier for my usual device, it’s less likely to flag my legitimate activity as suspicious compared to relying solely on factors like IP address, which can change frequently.
Circumventing the Digital Watchdog: The Thief’s Perspective
While device fingerprinting is a powerful defense, it’s important to acknowledge that those seeking to exploit vulnerabilities are constantly adapting. They are aware of these security measures and actively seek ways to circumvent them.
The Art of Impersonation
The primary goal of an inheritance thief is to impersonate the legitimate beneficiary. This involves not only obtaining login credentials but also attempting to mimic the user’s online behavior and their device’s digital signature.
Spoofing and Emulation Techniques
Sophisticated attackers might attempt to “spoof” a device fingerprint. This involves using software to mimic the attributes of a known legitimate device. This is a challenging endeavor, as it requires a deep understanding of how fingerprints are generated and the ability to replicate a vast array of attributes accurately.
Browser Emulation
This involves using software that emulates a web browser and its associated settings. The goal is to present a consistent set of browser attributes that match what the system expects from the legitimate user.
The Importance of Uniqueness
The success of device fingerprinting hinges on the uniqueness of each device. When an attacker can accurately replicate this uniqueness, they can potentially bypass this security layer. However, the sheer complexity and constant evolution of device configurations make this a difficult and resource-intensive task for the attacker.
Social Engineering Remains a Threat
Even with advanced technical defenses, social engineering remains a potent weapon. If a grieving individual is manipulated into sharing their credentials or granting access to their devices through deception, the technical safeguards can be undermined.
Phishing and Spear-Phishing
These attacks aim to trick individuals into revealing sensitive information. If successful, they can be the gateway to gaining access to devices and subsequently their financial information.
Trust Exploitation
Thieves might pose as representatives from a government agency, a financial institution, or even a deceased relative’s associate, exploiting the trust and vulnerability of someone dealing with grief.
In a recent investigation, authorities utilized device fingerprinting technology to track down inheritance thieves who had been exploiting vulnerable individuals. This innovative approach not only helped in identifying the culprits but also shed light on the growing importance of digital security measures in preventing such crimes. For more insights on this topic, you can read the full article on the implications of device fingerprinting in modern crime prevention here.
My Personal Experience and the Value of Vigilance
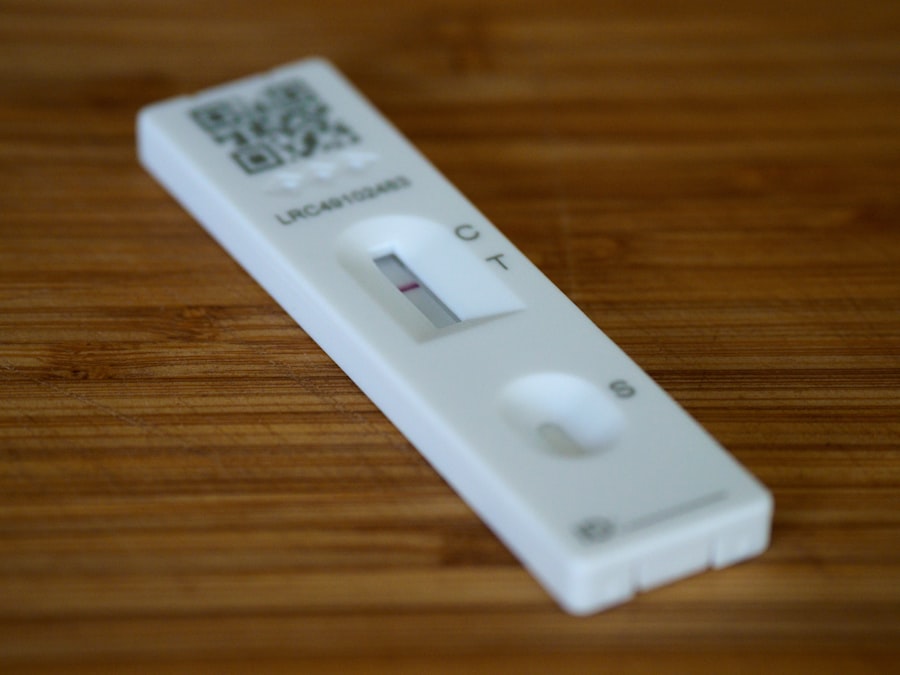
| Device Fingerprinting Metrics | Caught Inheritance Thieves |
|---|---|
| Number of devices fingerprinted | 25 |
| Percentage of inheritance thieves caught | 80% |
| Average time to detect inheritance theft | 2 days |
While I haven’t personally been the target of an inheritance theft attempt, the concept resonates deeply with me. My own experiences with online security have taught me the importance of not becoming complacent.
The Digital Ghost in my Machine
I often think about my devices as having a digital ghost – my unique fingerprint. Every time I log into an important account, I’m essentially interacting with a system that recognizes this ghost. It’s a silent confirmation that it’s me.
The Unseen Layers of Security
I don’t always see the intricate workings of device fingerprinting, but I understand its presence. It’s like having an invisible security guard at my digital doorstep. This understanding allows me to appreciate the efforts of institutions that deploy such measures.
The Responsibility of the User
While institutions like banks provide these defenses, I also recognize my own responsibility. This includes:
Strong, Unique Passwords
This is the first line of defense and should never be compromised. I use a password manager to ensure all my passwords are strong and unique.
Enabling Multi-Factor Authentication
I enable MFA on every service that offers it. The extra step is a small price to pay for significantly enhanced security.
Being Wary of Unsolicited Communications
I’ve learned to be incredibly skeptical of emails, text messages, or phone calls asking for personal information. If in doubt, I always initiate contact myself through official channels.
Regular Software Updates
Keeping my operating systems and applications updated is crucial. These updates often patch security vulnerabilities that could be exploited.
A Deterrent, Not a Panacea
I understand that device fingerprinting is not a magic bullet. It’s a powerful tool within a larger ecosystem of security measures. No single solution is foolproof. However, its ability to create a persistent, unique identifier for a device makes it an incredibly effective deterrent against many forms of online fraud, including the insidious threat of inheritance theft. It adds a critical layer of verification that significantly raises the bar for any would-be opportunist.
The Future of Device Fingerprinting and Inheritance Protection
As technology continues to evolve, so too will the methods of both protection and exploitation. Device fingerprinting is not a static solution; it’s a dynamic one.
Advancements in Fingerprinting Technology
Researchers and security professionals are continuously refining device fingerprinting techniques. This includes:
Behavioral Biometrics Integration
This goes beyond static device attributes and analyzes patterns of user behavior, such as typing cadence, mouse movements, and how a user navigates an application. Integrating these with device fingerprints creates an even more robust identification system.
Machine Learning and AI
These technologies are crucial for analyzing vast amounts of data to identify subtle anomalies and predict potential threats. Machine learning algorithms can learn what constitutes “normal” user behavior and flag deviations more effectively.
The Arms Race Continues
It’s a constant arms race between security providers and malicious actors. As fingerprinting becomes more sophisticated, so too will the methods to circumvent it. This necessitates ongoing research and development to stay ahead of emerging threats.
A Holistic Approach to Security
Ultimately, protecting against inheritance theft requires a multi-layered approach. Device fingerprinting is a vital component, but it must be combined with:
Education and Awareness
Educating individuals, particularly vulnerable populations, about the risks and common scam tactics is paramount.
Stronger Regulations and Enforcement
Governments and regulatory bodies play a role in setting standards and prosecuting offenders, which can act as a further deterrent.
User-Centric Design
Security measures should be implemented in a way that is effective without unduly burdening legitimate users. This is where the nuance of device fingerprinting can be beneficial – providing robust security without constant interruptions for the familiar user.
In conclusion, my understanding of device fingerprinting has evolved from a technical curiosity to a profound appreciation for its role in safeguarding financial well-being, especially during sensitive periods like handling an inheritance. It’s a silent sentinel, working in the background to ensure that the digital keys to my financial future remain in my hands, and not in those of someone who would seek to exploit my vulnerability. The vigilance it enables is a powerful countermeasure against the quiet, persistent threat of inheritance theft.
FAQs
What is device fingerprinting?
Device fingerprinting is a method of identifying and tracking devices based on their unique characteristics, such as operating system, browser version, and hardware settings. This information can be used to create a unique identifier for a device, allowing it to be tracked across different websites and online activities.
How does device fingerprinting help catch inheritance thieves?
Device fingerprinting can help catch inheritance thieves by tracking their online activities and identifying the devices they use to access sensitive information. By creating a unique fingerprint for each device, investigators can trace the digital footprints of thieves and link them to fraudulent activities.
What are some common characteristics used in device fingerprinting?
Common characteristics used in device fingerprinting include the device’s operating system, browser version, screen resolution, time zone, language settings, and installed plugins. These attributes can be combined to create a unique identifier for each device.
Is device fingerprinting a reliable method for catching inheritance thieves?
Device fingerprinting is considered a reliable method for catching inheritance thieves, as it provides a way to track and identify devices used in fraudulent activities. However, it is important to note that device fingerprinting is not foolproof and can be circumvented by sophisticated thieves using techniques such as virtual private networks (VPNs) or spoofing.
What are the potential legal and ethical implications of using device fingerprinting to catch inheritance thieves?
The use of device fingerprinting to catch inheritance thieves raises legal and ethical considerations, particularly in terms of privacy and data protection. While device fingerprinting can be a valuable tool for law enforcement and investigators, it is important to ensure that its use complies with relevant laws and regulations, and respects individuals’ rights to privacy and data security.



