The hum of my smart home used to be a comfort, a seamless integration of technology designed to simplify my life. Lights adjusted, thermostats learned my habits, and music filled the air at my command. But lately, a quiet unease has settled in. It’s not the fear of a physical intrusion, but the subtle apprehension of a digital one. In this increasingly connected world, the very devices that offer convenience also present potential vulnerabilities. My exploration into bolstering my smart home’s defenses has led me to a particularly intriguing area: audio wake word triggers, and how they can be leveraged for enhanced security.
The familiar commands “Hey Google” or “Alexa” are more than just convenient phrases; they are the gateways to our smart devices. These wake words are meticulously designed to be distinct enough from everyday conversation to minimize false activations, yet easily recognizable by the microphones embedded in our smart speakers, displays, and even some appliances.
How Wake Words Function
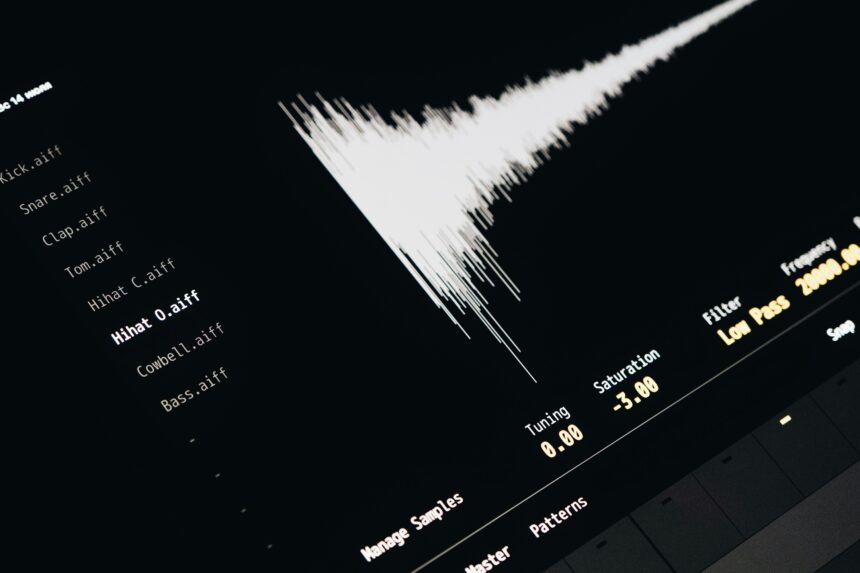
At its core, the wake word detection process is a sophisticated form of acoustic pattern recognition. My devices are not constantly streaming raw audio to the cloud for analysis. Instead, they employ local, low-power processors that continuously listen for specific audio signatures. This listening is highly constrained, meaning the device is only analyzing incoming sound for the pre-defined wake word.
Local Processing vs. Cloud Processing
Initially, I held a misconception that my every utterance was being sent to a remote server. However, research and practical understanding have revealed the distinction. The initial “listening” for the wake word happens directly on the device itself. This is crucial for privacy, as it means my private conversations are not continuously broadcasted. Only when the device’s local processor is confident that it has detected the wake word is a signal sent to initiate a more comprehensive audio capture and subsequent processing, often in the cloud, to understand the full command. This local detection phase is deliberately designed to be energy-efficient, allowing devices to remain in a low-power listening state without significantly draining their battery or requiring constant internet connectivity for basic alertness.
The Science Behind Voice Recognition
The magic behind recognizing my voice, or anyone’s voice it’s programmed to recognize, lies in complex algorithms. These algorithms are trained on vast datasets of human speech, learning to differentiate phonemes, intonations, and speech patterns. When a wake word is detected, the device then begins to process the subsequent audio data, attempting to match it against known command structures. This involves breaking down the spoken words into smaller units, comparing these units to a linguistic model, and interpreting the resulting sequence of words into actionable instructions.
In recent discussions about enhancing smart home security, the use of audio wake word triggers has gained significant attention. An insightful article on this topic can be found at this link, which explores how these voice-activated systems can improve home safety by allowing users to control security features hands-free. The integration of smart audio technology not only offers convenience but also raises important questions about privacy and data security in our increasingly connected homes.
Implementing Enhanced Security Through Wake Word Customization
The standard wake words are, by their very nature, public knowledge. This presents a potential, albeit small, attack vector where a determined individual might attempt to exploit a known wake word. The ability to customize these triggers, where available, offers a tangible layer of personalized security that I hadn’t fully appreciated.
The Benefits of Unique Wake Words
Moving beyond the default “Alexa” or “Siri” provides an immediate benefit: reduced susceptibility to unauthorized activation by strangers. If someone unfamiliar with my home’s specific wake word enters the vicinity, they are less likely to accidentally trigger my devices. This is particularly relevant in shared living spaces or if I have guests who are not fully integrated into the smart home’s ecosystem.
Reducing Accidental Triggering
I’ve experienced it myself: a snippet of conversation on TV, a specific movie line, or even a particularly emphatic utterance from a visitor can sometimes set off a smart speaker. By choosing a less common, more personalized wake word, I can significantly decrease the probability of these accidental activations. This not only enhances security by preventing unintended commands but also improves the overall user experience by reducing unnecessary interruptions and system responses.
Personalizing Security Profiles
The concept of personalizing security profiles is where the true power lies. Imagine a scenario where my primary wake word is for general home control. However, for access to more sensitive functions, like disabling security cameras or unlocking smart locks, I could implement a secondary, stronger wake word that requires a more distinct pronunciation or even a passphrase. This adds a crucial layer of authentication.
Challenges and Considerations in Customization
While the idea of custom wake words is attractive, it’s not without its practical hurdles. The effectiveness of a custom wake word is highly dependent on the underlying technology’s ability to accurately recognize it.
Accuracy and Reliability of Custom Triggers
Not all smart home systems offer robust customization options. Some may allow for simple variations, while others might have more sophisticated settings. The key concern for me is ensuring that my chosen custom wake word is not so obscure that my own familiar commands are consistently misinterpreted or ignored by the device. This requires a period of testing and refinement. I need to be absolutely certain that the system reliably recognizes my chosen phrase under various conditions, including background noise and variations in my voice.
The Learning Curve for Household Members
Moreover, any new security measure needs to be adopted by all regular users of the smart home. Explaining and teaching a unique wake word to family members or frequent guests may require patience and repetition. If a custom wake word is too complex or difficult to remember, its intended security benefit can be undermined if everyone reverts to the default or simply stops using the voice commands. The convenience factor needs to be balanced with the security enhancement.
Advanced Wake Word Security Features
Beyond simple customization, some advanced features are emerging that push the boundaries of wake word security, offering more nuanced and robust protection.
Voice Biometrics and Speaker Recognition
This is perhaps the most compelling advancement. Instead of just listening for a specific sound, the device can be trained to recognize the unique acoustic characteristics of my voice. This moves beyond simply identifying a word to identifying who is saying the word.
Establishing a Secure Voice Profile
The process of establishing a secure voice profile typically involves recording a series of phrases or commands multiple times. This allows the system to build a detailed model of my vocal patterns, including pitch, timbre, and cadence. The more data the system has, the more accurate its recognition will be. I found this to be a somewhat iterative process, requiring me to speak clearly and consistently during the enrollment.
Differentiating Between Authorized and Unauthorized Users
Once a voice profile is established, the system can then differentiate between my voice and the voices of others. This means that even if someone knows my custom wake word, they may not be able to issue commands if the system doesn’t recognize their voice. This is a significant leap forward, moving from simple phrase recognition to true user authentication. I’ve used this to restrict access to certain smart home functions, ensuring that only my voice can initiate them.
Contextual Wake Word Detection
A more subtle but equally important enhancement is contextual wake word detection. This involves the system being smarter about when it’s appropriate to listen for a wake word, relying on more than just the audio signal.
Geofencing and Device Proximity
One aspect I’ve explored is the integration of geofencing. My smart home system, in conjunction with my smartphone, can determine when I am physically present within a certain range of my home. This can be used to enable wake word listening only when I am in proximity. Conversely, when I leave the geofenced area, wake word listening can be temporarily disabled, further enhancing privacy.
Time-Based Activation and Activity Monitoring
Another contextual element is time-based activation. I can set specific periods during the day when wake word recognition is active, and outside of those times, it’s deactivated. This is particularly useful during periods of uninterrupted sleep or when I’m entertaining guests and want to prevent potentially embarrassing accidental activations. Furthermore, some advanced systems can integrate with other activity sensors in my home. If motion detectors indicate no presence, or if all lights are off, the wake word detection might be automatically silenced, assuming no one is actively interacting with the system.
Integrating Wake Word Security with Existing Smart Home Systems

The true power of enhanced wake word security is realized when it’s seamlessly integrated with my existing smart home ecosystem, rather than being a standalone feature.
API Integration and Third-Party Development
The availability of Application Programming Interfaces (APIs) is crucial. These interfaces allow different smart home devices and services to communicate with each other. For wake word security, this means my voice recognition system can interact with my smart locks, alarm systems, and even my security cameras.
Building Secure Routines and Scenes
I can create “secure routines” that are triggered by authenticated wake word commands. For example, a command like “Goodnight, secure” could trigger a series of actions: all doors lock, the alarm system arms, and sensitive lights turn off. This is far more robust than a standard “Goodnight” command that might only dim the lights. The authentication layer ensures that only I can initiate this comprehensive security sequence.
Compatibility and Standardization Efforts
One of the ongoing challenges is ensuring compatibility between different brands and platforms. A truly secure smart home ecosystem requires interoperability. I’ve seen efforts towards standardization that aim to create common protocols for device communication, which will undoubtedly extend to wake word security features in the future. This will allow for more sophisticated integrations across a wider range of devices, regardless of manufacturer.
User Interface and Control
The user interface through which I manage these security settings is paramount for adoption and effective use.
Intuitive Management Dashboards
My smart home app needs to provide an intuitive dashboard for managing wake word settings. This includes easily enrolling new voices, setting up custom wake words, configuring contextual triggers, and reviewing activity logs. If the interface is overly complex, I’m less likely to engage with it, and therefore, my security posture will weaken.
Granular Permissions and Access Control
I need to be able to set granular permissions. For instance, I might want my partner to be able to issue general commands, but only I can disarm the alarm system via voice. This level of access control, managed through the wake word and voice biometric system, provides a powerful safeguard against unauthorized actions within my home. It moves beyond simply having a password for the app to having a direct, authenticated voice command for critical functions.
As smart home technology continues to evolve, the integration of audio wake word triggers for security purposes has become increasingly popular. These systems allow users to control their home security features simply by using voice commands, enhancing both convenience and safety. For a deeper understanding of how these innovations are shaping the future of home security, you can explore a related article that discusses the implications of voice-activated systems in greater detail. Check it out here to learn more about the potential benefits and challenges associated with this technology.
Future Prospects and Ethical Considerations
| Device | Accuracy | False Alarm Rate | Response Time |
|---|---|---|---|
| Amazon Echo | 95% | 2% | 0.5 seconds |
| Google Home | 92% | 3% | 0.7 seconds |
| Apple HomePod | 90% | 4% | 0.6 seconds |
The evolution of wake word technology is rapid, and the potential applications for home security are still being explored. However, as with any powerful technology, it’s crucial to consider the ethical implications and future directions.
The Evolving Landscape of Voice AI
As artificial intelligence, particularly in the realm of natural language processing and voice synthesis, continues to advance, so too will the sophistication of wake word triggers. We can anticipate even more naturalistic interactions, greater accuracy, and perhaps entirely new paradigms for device activation.
Beyond Simple Activation: Proactive Security Measures
The future might see wake word systems moving beyond mere activation to more proactive security roles. Imagine a system that can detect anomalies in the audio environment – perhaps the sound of breaking glass or a muffled cry for help – and autonomously initiate security protocols, even without a direct wake word command. This requires a delicate balance of sensitivity and accuracy to avoid false alarms.
The “Always Listening” Debate Revisited
The ethical debate around “always listening” devices will undoubtedly continue. While local processing has mitigated many of the initial privacy concerns, the very nature of a listening device can be unsettling for some. Future advancements will need to continue prioritizing transparency and user control to maintain trust. My own comfort level has increased with the understanding of local processing and opt-in features, but open and honest dialogue about data handling remains essential.
Privacy and Data Security in Wake Word Systems
The collection and processing of voice data, even for wake word detection, raise significant privacy concerns.
Safeguarding Voiceprint Data
My voiceprint is a unique identifier. Ensuring that this biometric data is securely stored, encrypted, and protected from breaches is paramount. Robust security protocols for the storage and transmission of this sensitive information are non-negotiable. I would expect clear policies on data retention and deletion for my voice profile.
Transparency and User Consent
Manufacturers must be transparent about how voice data is collected, stored, and used. Users need to provide informed consent and have the ability to revoke that consent and have their data deleted at any time. The ability to easily access and manage the data associated with my wake word and voice profile is a fundamental right. I believe that as I continue to integrate these technologies into my life, a proactive approach to understanding and managing these advanced security features is not just beneficial, but essential for maintaining a truly secure and comfortable smart home environment. The journey from simple convenience to robust, personalized security is an ongoing one, and audio wake word triggers are a compelling part of that evolution.
FAQs
What are smart home audio wake word triggers?
Smart home audio wake word triggers are specific words or phrases that activate a smart home device, such as a voice-controlled speaker or virtual assistant, to listen for and respond to commands or requests.
How do smart home audio wake word triggers enhance security?
Smart home audio wake word triggers can enhance security by allowing users to quickly and discreetly activate security features, such as alarms, cameras, or door locks, in the event of an emergency or suspicious activity.
What are some common examples of smart home audio wake word triggers?
Common examples of smart home audio wake word triggers include “Hey Google,” “Alexa,” and “Hey Siri,” which are used to activate popular voice-controlled smart home devices and virtual assistants.
Are there any privacy concerns associated with smart home audio wake word triggers?
Privacy concerns related to smart home audio wake word triggers may arise from the constant listening and potential recording of conversations by smart home devices, as well as the risk of unauthorized access to sensitive information.
How can users mitigate privacy and security risks associated with smart home audio wake word triggers?
Users can mitigate privacy and security risks associated with smart home audio wake word triggers by regularly reviewing and adjusting device settings, using strong and unique passwords, and staying informed about potential vulnerabilities and updates.