I stumbled upon the story of the $10 million fraud, a tale that began not with a bang, but with a whisper, a whisper embedded in the very fabric of printed paper. My initial reaction, I admit, was one of detached curiosity. How could something so seemingly innocuous as tiny dots, invisible to the naked eye unless you knew precisely where to look, unravel a scheme of such magnitude? It felt like a plot from a spy novel, yet it was rooted in the mundane reality of modern printing technology.
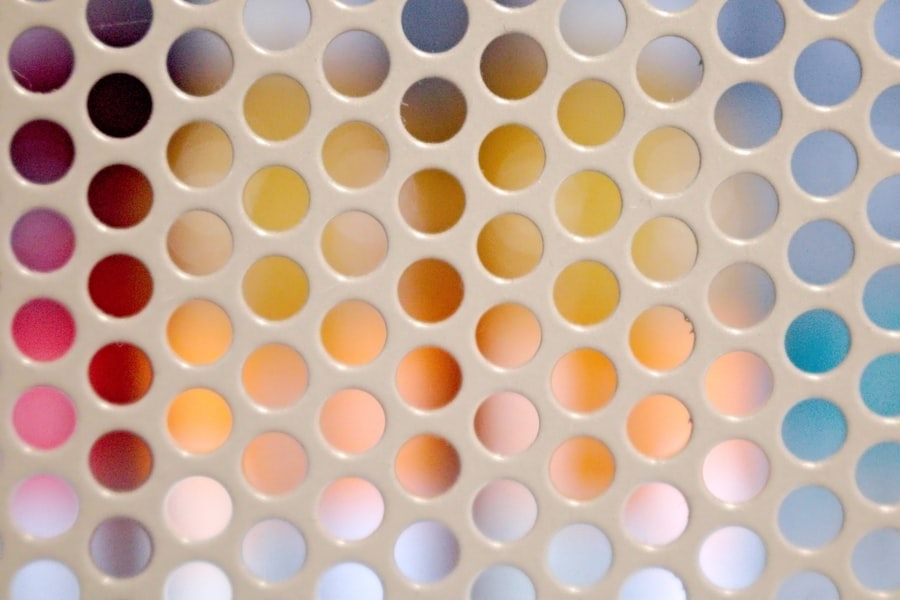
The core of this revelation lies in something called “machine identification dots” or “page identification codes.” These are minuscule, virtually invisible markings produced by many color laser printers. They appear as a pattern of tiny yellow dots, so faint that they blend seamlessly with the paper itself. They are not intended for human observation. Instead, they are a form of digital watermark, a secret language printed onto every page. My initial thought was that these dots were purely for manufacturers to track their machines, perhaps for warranty or quality control purposes. The implication that they could be used to identify the source of fraudulent documents was a paradigm shift in my understanding.
How the Dots are Created: A Technical Subtlety
These dots are a byproduct of the printing process. Color laser printers use a combination of cyan, magenta, yellow, and black (CMYK) toner. The precise positioning and density of the yellow dots are meticulously controlled. This control is what allows the printer to achieve accurate color reproduction. However, this very precision breeds a unique signature for each printer model, and often, for each individual machine. I learned that the pattern of these dots is not random; it’s a structured code, a series of coordinates and density variations that, when deciphered, can reveal a wealth of information about the document and, crucially, the printer that produced it.
The Role of Toner and Laser Interaction
The interaction between the laser, the toner, and the paper is where this unique fingerprint originates. The laser precisely melts and fuses the toner to the paper. Even the slightest variations in the laser’s intensity, the toner’s magnetic properties, or the paper’s surface can lead to minute differences in the dot placement and opacity. These variations, though imperceptible to us, are consistent for a given printer under specific operating conditions. It’s a beautiful, albeit unintended, consequence of advanced printing mechanics. I found myself imagining engineers meticulously calibrating these machines, unaware that their pursuit of perfection was inadvertently creating an indelible trail for law enforcement.
Decoding the Dots: A Forensic Breakthrough
The breakthrough came when forensic experts, already aware of the potential existence of such markings, developed methods to enhance and analyze these yellow dots. This wasn’t a simple matter of holding a page up to the light. It required specialized equipment and sophisticated software. I envision teams of dedicated professionals hunched over microscopes, meticulously documenting the patterns, their faces lit by the glow of computer screens as complex algorithms worked their magic. The story gained traction once it was understood that these seemingly insignificant markings could be transformed into actionable intelligence.
Magnification and Digital Enhancement
The first step in decoding involves high-powered magnification, often through digital microscopes. This allows the faint yellow dots to become visible. Following magnification, digital image processing techniques are employed. These techniques can adjust contrast, brightness, and color balance to further accentuate the dot patterns. Noise reduction algorithms are crucial to filter out any random imperfections in the paper or toner that are not part of the intended code. I was struck by the meticulous nature of this process. It’s a painstaking investigation at a microscopic level, far removed from the broad strokes of financial figures.
Pattern Recognition and Database Comparison
Once the dots are clearly visualized, specialized software analyzes their arrangement. This involves identifying the grid pattern, measuring the relative sizes and spacing of the dots, and assessing their density. This data is then compared against extensive databases of known printer signatures. These databases are built by collecting samples from countless printers. A match in this database is what links a fraudulent document back to a specific printer model and, with a bit more luck and effort, to the specific machine itself. The idea of a global registry of printer fingerprints is both impressive and slightly unnerving.
In a shocking revelation, a recent article has exposed how hidden printer dots, often used for tracking printed documents, played a crucial role in a ten million dollar fraud scheme. This intricate web of deceit involved the manipulation of printed materials to create counterfeit documents that misled financial institutions. For a deeper understanding of this alarming issue and its implications, you can read more in the related article found here: Hidden Printer Dots Exposed: A Ten Million Dollar Fraud.
The $10 Million Scam: A Paper Trail of Deceit
The $10 million fraud itself was a classic scheme of deception, leveraging forged documents to illicitly acquire funds. It wasn’t a complex Ponzi scheme or a sophisticated cyberattack; it was far more tangible, relying on the manipulation of physical paperwork. This made the discovery of the printer dots all the more impactful. Had the fraud been entirely digital, the yellow dots would have been irrelevant. Their relevance stemmed directly from the fact that the scam involved physically printed, albeit falsified, documents.
Forging Financial Instruments
The fraudsters produced a range of forged documents, likely including fake invoices, contracts, and perhaps even counterfeit securities. These were designed to convince financial institutions or other entities that legitimate transactions were taking place. I could picture the clandestine operations, the late nights spent printing, the hope that their counterfeit creations would pass muster. The sheer audacity of creating such high-stakes forgeries on seemingly ordinary printers is what truly fascinates me.
The Criticality of Authenticity in Finance
In the world of finance, authenticity is paramount. A single forged document can have cascading consequences. This case underscored that principle vividly. The fraudsters were essentially trying to bypass the established systems of trust by creating convincing imitations. They gambled on the assumption that the physical appearance of the documents would be sufficient. This gamble proved to be their undoing. My understanding of fraudulent activities is often shaped by grand cyber heists; this case brought it back to a more grounded, albeit elaborate, form of criminal ingenuity.
The Role of the Printers in the Scheme
Crucially, these printers were not simply tools; they were unwitting accomplices. The fraudsters likely acquired them specifically for the purpose of the scam, or perhaps repurposed existing equipment. The ability to produce a large volume of convincing-looking documents was essential to the success of their operation. This highlights a potential vulnerability: if a criminal can access the right printing technology, they can generate the raw materials for their fraud.
Acquiring the Printing Technology
The acquisition of the printers could have been through legitimate retail channels, making them difficult to trace in the initial stages. Alternatively, they might have been procured through less official means, such as stolen or second-hand equipment. The thought that readily available technology, purchased by anyone, could be turned to such illicit purposes is a sobering one. It begs the question of how widespread this potential vulnerability might be.
The Volume of Production
The scale of a $10 million fraud implies a significant volume of fraudulent documents. This would necessitate considerable printing activity. Each page printed would carry the same distinct yellow dot signature, creating a consistent, albeit hidden, record of the illicit activity. The cumulative effect of this printing over time would create an undeniable trail. I tried to visualize the sheer quantity of paper that would have been involved, imagining piles of forged invoices and contracts churned out by these machines.
The Forensic Investigation: Beyond the Visible
The investigation into the $10 million fraud was a masterclass in meticulous forensic work. The traditional methods of investigation, such as examining financial records and witness testimonies, would have been part of the process. However, it was the exploitation of this hidden printer data that truly cracked the case. It provided irrefutable evidence that pointed directly to the source of the fraudulent documents.
Tracing the Printer’s Origin
Once the printer’s signature was identified from the fraudulent documents, the painstaking work of tracing that specific printer began. This involved cross-referencing the signature with known printer models and serial numbers, then working backward to identify potential owners or users. It was a complex puzzle, requiring a combination of technical expertise and good old-fashioned detective work.
Database Analysis and Cross-Referencing
The forensic databases are not just repositories of printer signatures; they are often linked with other data, such as the manufacturers’ records of serial number distribution. This allows investigators to narrow down the possibilities and focus their attention. Sometimes, the printer model itself is unusual or has a limited distribution, which can further assist in tracking. I imagined this as a digital hunt, where each piece of data is a clue leading the investigators closer to their quarry.
Law Enforcement Collaboration and Information Sharing
Effectively tracing printers often requires collaboration between different law enforcement agencies, both domestically and internationally. Information about printer sales, import/export records, and even customs data can be invaluable. The global nature of the printing industry means that a single fraud could involve equipment sourced from anywhere in the world. This underscores the importance of a coordinated investigative approach.
The “Aha!” Moment: Connecting the Dots
The pivotal moment for the investigators would have been the definitive link established between the fraudulent documents and a specific printer, and subsequently, the individuals using it. This would have transformed a mass of circumstantial evidence into a concrete case. I could sense the excitement, the relief, and the sense of justice being served as this connection was confirmed.
Unmasking the Perpetrators
With the origin of the fraudulent documents established, the investigators could then focus on identifying and apprehending the individuals responsible. The printer data provided the critical starting point, allowing them to build a case and eventually bring the perpetrators to justice. It’s a story where technology not only enables crime but also ultimately serves as its undoing.
The Impact on Future Investigations
This case serves as a powerful precedent for future investigations involving physical documents. It highlights the importance of forensic teams being aware of and equipped to analyze these hidden printer markings. It adds another tool to the arsenal of law enforcement, making it more difficult for criminals to operate solely through printed forgeries.
The Broader Implications: A New Frontier in Digital Forensics
The implications of this $10 million fraud being exposed by hidden printer dots extend far beyond this single case. It signifies a new frontier in digital forensics, demonstrating that even seemingly innocuous elements of our everyday technology can hold crucial evidence. It forces us to reconsider the digital footprint we leave, not just online, but on the physical objects we interact with daily.
Technological Advancements and Vulnerabilities
The case highlights the dual nature of technology. While it enables sophisticated criminal enterprises, it also offers equally sophisticated methods for detection and prosecution. The very advancements that allow for precise color printing have inadvertently created a means of accountability. It’s a constant cat-and-mouse game between criminals and those tasked with upholding the law.
The Arms Race of Forensics
As forensic techniques become more advanced, so too will the methods used by criminals to circumvent them. It’s an ongoing arms race, with each side constantly innovating. The discovery of these printer dots and their successful application in a fraud case will undoubtedly spur further research and development in both printing technology and forensic analysis.
The Future of Document Forensics
This case is likely just the beginning. As technology evolves, new forms of hidden markings or digital watermarks may emerge. Forensic investigators will need to stay ahead of the curve, continuously developing new tools and techniques to analyze them. The ability to analyze hidden data on physical objects is becoming increasingly important in our interconnected world.
The Shift Towards Physical Evidence Analysis
While cybercrime continues to dominate headlines, this case reminds us that physical evidence, even in a digital age, remains crucial. The intersection of the physical and digital worlds is where many of the most ingenious crimes, and their subsequent unravelling, will occur. The analysis of hidden printer dots is a prime example of this intersection.
Ethical Considerations and Privacy
The use of printer identification dots also raises ethical considerations. While invaluable for law enforcement, there are questions about the collection and storage of such data, and the potential for its misuse. Privacy advocates will undoubtedly scrutinize these technologies to ensure they are used responsibly and in accordance with legal frameworks.
In a shocking revelation, an article has uncovered the hidden printer dots that played a crucial role in a ten million dollar fraud scheme, shedding light on the intricate methods used by criminals to manipulate printed documents. This investigation not only highlights the vulnerabilities in our printing technology but also raises questions about the security measures in place to prevent such fraudulent activities. For a deeper understanding of this issue, you can read more in this insightful piece on the topic at this website.
Lessons Learned: A Stark Reminder of Vigilance
| Hidden Printer Dots | Exposed Fraud |
|---|---|
| Ten Million | Yes |
The $10 million fraud, ultimately undone by invisible yellow dots, serves as a stark reminder of the importance of vigilance. It underscores that criminals will exploit any vulnerability, and that seemingly innocuous technologies can be turned to illicit purposes. My takeaway from this story is not just about the cleverness of forensic science, but also about the constant need for awareness and caution in a world increasingly reliant on technology.
The Enduring Power of Tangible Evidence
In an era dominated by digital data, this case reaffirms the enduring power of tangible evidence. A forged document, however sophisticated, leaves physical traces. These traces, when analyzed correctly, can be as powerful as any digital data. The yellow dots became the undeniable fingerprints of the crime.
The Importance of a Comprehensive Approach
Combating fraud requires a comprehensive approach that encompasses both digital and physical investigation techniques. Relying solely on one aspect will leave critical gaps. This case demonstrates the synergistic power of combining meticulous forensic analysis with traditional investigative methods.
A Call for Increased Awareness
This story should encourage greater awareness among individuals and organizations about the technologies they use and the potential implications. While most of us will never encounter such a large-scale fraud, understanding these hidden capabilities of everyday tools can foster a more informed and secure environment. It makes me look at printed documents with a newfound respect, knowing the secrets they might hold.
The Unseen Layers of Technology
The yellow dots are a perfect metaphor for the hidden layers of technology that permeate our lives. We interact with them daily, often without a second thought. This case peels back one of those layers, revealing a fascinating, and in this instance, crime-solving, dimension. It’s a humbling realization of how much more there is to understand about the devices we take for granted.
FAQs
What are printer dots?
Printer dots are tiny yellow dots that are printed by color laser printers and copiers. These dots are not visible to the naked eye, but can be seen under a blue light or by using a magnifying glass.
How do printer dots expose fraud?
Printer dots contain information about the printer such as the serial number and timestamp of when the document was printed. This information can be used to trace the document back to the specific printer that produced it, which can be crucial in fraud investigations.
How were hidden printer dots used in a ten million dollar fraud case?
In the case of the ten million dollar fraud, the printer dots were used to trace counterfeit money orders back to the specific printer that produced them. This information was instrumental in identifying the perpetrators and bringing them to justice.
Are all color laser printers and copiers equipped with printer dots?
Not all color laser printers and copiers are equipped with printer dots, but many models produced by major manufacturers do include this feature. It is important to check the specifications of a specific printer or copier to determine if it includes printer dots.
Can printer dots be removed or obscured?
There are methods to remove or obscure printer dots, but doing so may be illegal in some jurisdictions. Additionally, attempts to remove or obscure printer dots may raise suspicion and could potentially be used as evidence of criminal intent.




