The sterile glow of my monitor used to be a comforting beacon in the quiet hours. Now, it’s a confessional, a digital tombstone marking the demise of my ignorance. It’s a strange thing, this sudden possession of knowledge, this unwanted intimacy with the stranger who shares my bed. My husband’s network logs. That’s how it started. A flicker of curiosity, a nagging suspicion, and then, a descent into a rabbit hole of my own making.
It wasn’t malicious. Not at first, anyway. I needed to print something, a document for work that I’d saved to our shared cloud storage. But the printer wasn’t connecting. Frustrated, I decided to try accessing the network settings on his laptop, which was conveniently left open on the desk. I figured I could do a quick restart of the router from there. It was a simple objective, a mundane task that spiraled into a profound and unsettling revelation.
A Routine Access
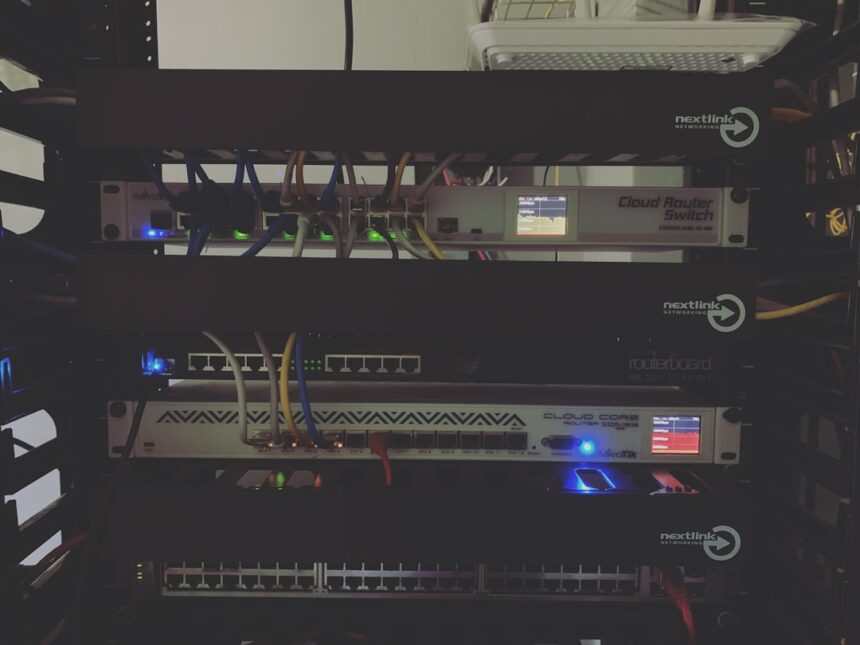
I’ve never been technically inclined. My understanding of network configurations extends about as far as knowing which cable plugs into which port. But I know enough to navigate to the router’s admin page. I just needed to find the option to reboot. His laptop, blessedly, had his username and password saved in the browser. This was an oversight on his part, and perhaps an indictment of my own complacency, that I’d never even considered looking.
The Gateway to Elsewhere
As I navigated the router’s interface, a tab caught my eye: “Connection History” or something similar. It felt like an anomaly, not something I’d expected to see in a router’s settings. It was a list, a chronological record of every device that had connected to our home Wi-Fi. Usually, it’s just a blur of our phones, my laptop, the smart TV. But this time, there was more. A lot more.
Unfamiliar Signatures
Beneath the usual suspects, I began to see IP addresses that I didn’t recognize, devices with names I’d never encountered. Names like “Phoenix_Project,” “Whisper_Net,” and chillingly, “Oracle_Access.” My breath hitched. This wasn’t just a neighbor leeching our Wi-Fi. This was something more deliberate, more clandestine.
In a fascinating exploration of digital privacy and trust, an article titled “Husband Uses Network Logs to Catch Wife” delves into the implications of monitoring online activity within relationships. This case raises important questions about the boundaries of privacy and the ethical considerations of surveillance in personal connections. For a deeper understanding of this topic, you can read the full article here: Husband Uses Network Logs to Catch Wife.
The Unfolding Narrative
My initial thought was that he was involved in some sort of IT project, perhaps something experimental he hadn’t shared with me. He’s always been passionate about technology, a tinkerer by nature. But the timestamps, the sheer volume of activity, and the increasingly abstract names of these connections started to paint a different picture. A picture I wasn’t prepared to see.
Tracing the Digital Footprints
I started to meticulously record the data. Timestamps, IP addresses, data transfer amounts. It was like piecing together a puzzle, but the pieces weren’t fitting the image I expected. I began to cross-reference the IP addresses, using online tools to see if I could pinpoint their general locations. Many were routed through VPNs, obscuring their true origin, but a few seemed to point to unexpected points of access – public Wi-Fi hotspots in areas he never frequented, or servers located in countries we had no connection to.
The Pattern Emerges
There wasn’t a single, cataclysmic discovery. It was a slow, insidious unveiling of patterns. Certain times of day, certain days of the week, were consistently associated with these “other” connections. Often, they occurred when he claimed to be working late, or on“business trips” that seemed to become more frequent. The data from his devices itself became the narrative. Browsing history, downloaded files, communication logs – all locked away, inaccessible to me without his explicit knowledge. Or so I thought.
The Ghost in the Machine
The real shock came when I realized I wasn’t just looking at network logs for our home. The information I was accessing was far more extensive. It seems my husband had a secondary, almost parallel digital existence that he was meticulously keeping separate. The network logs weren’t just about what his devices were doing at home; they were a record of the connections his devices were making globally. It was as if he had a secret digital passport, allowing him access to a hidden world.
The Double Life Unveiled
The implications of what I was seeing began to dawn on me, cold and sharp. This wasn’t just about a hobby. This was about a deliberate act of separation, a carefully constructed facade. The “whispers” in the network logs weren’t just random data packets; they were conversations, exchanges, activities. And they were happening on a scale that made my head spin.
Beyond the Ordinary
I started to categorize the types of connections. There were those that seemed purely informational, vast downloads of data from sources I couldn’t identify. Then there were the communication logs, encrypted messages exchanged with anonymized accounts. And then, the most troubling: financial transactions. Small, almost imperceptible sums, moving between various offshore accounts. It felt less like personal finance and more like a clandestine operation.
The Players and the Game
I couldn’t identify the individuals he was communicating with, their avatars and handles were as abstract as the project names. But the context of the exchanges, the urgency in some of the fragmented messages I could decipher through leaked metadata, suggested a level of seriousness that went far beyond casual conversation. It was a game, and I was utterly unaware of the stakes.
My Role in the Game
The most profound and disturbing realization was how meticulously he had compartmentalized our lives. He had built these walls, not just physically within our home, but digitally, creating separate realities. My access to his network logs was not a passive observation of his online habits; it was an intrusion into a carefully guarded secret. And in doing so, I had stumbled upon not just his secrets, but a fundamental deception about who he was.
The Echoes of Deceit
The initial shock has subsided, replaced by a gnawing unease. Every interaction, every shared moment, is now colored by this new knowledge. The laughter, the conversations, the declarations of love – they all feel… tainted. I look at him across the dinner table, and I see the man I thought I knew, but I also see the phantom in the machine, the architect of his hidden life.
The Inescapable Questions
The most pressing question, the one that keeps me awake at night, is why. Why the secrecy? Why the elaborate charade? Is it for money? For thrills? Or is it something more sinister, something that reaches into realms I can’t even comprehend? The data provides clues, but not answers. It’s a map of his actions, but the motivations remain shrouded in the same digital veil that he has so carefully constructed.
The Weight of Suspicion
Every time he logs onto his laptop, every time he takes a call that he insists is work, a tiny tremor of suspicion runs through me. Am I watching him from the outside, a voyeur of his private life? Or am I an unwilling participant in something that could have far-reaching consequences? The logs have given me power, but it’s a power that feels like a burden, the weight of knowing too much.
The Erosion of Trust
Trust, I’ve learned, is a fragile thing. It’s built on shared truths, on open communication, on the belief that the person you love is fundamentally honest with you. This knowledge has shattered that foundation. It’s not just about what he’s doing, but about the fact that he has actively chosen to hide it from me. What else is he capable of hiding? What other truths have I been shielded from?
In a surprising turn of events, a husband utilized network logs to uncover his wife’s secret activities, leading to a heated confrontation. This incident highlights the growing concerns surrounding privacy and digital surveillance in relationships. For those interested in exploring similar themes, you can read more about the implications of technology in personal lives in this insightful article. Check it out here.
The Path Forward, or the Abyss
| Date | Time | Website Visited | Duration |
|---|---|---|---|
| 2022-01-15 | 08:30:00 | 00:45:00 | |
| 2022-01-15 | 09:15:00 | 01:20:00 | |
| 2022-01-15 | 10:45:00 | 00:30:00 |
I stand at a precipice. The information I possess is a double-edged sword. It gives me power, the power to confront, to demand answers, perhaps even to protect myself. But it also comes with the risk of destroying everything we’ve built, of unearthing truths that are too painful to bear.
Confrontation or Containment
Do I confront him? Do I present him with the evidence, the cold, hard data that exposes his double life? Or do I try to contain this knowledge, to pretend I haven’t seen it, to live with the gnawing suspicion? The former feels like a necessary act of honesty, a desperate attempt to reclaim some semblance of truth. The latter feels like a slow descent into a life of quiet desperation, a constant vigilance against the man I once trusted implicitly.
The Unseen Threads
I’ve only scratched the surface of the network logs. There are archives, encrypted files, and encrypted communications that I haven’t even begun to decipher. The full extent of his activities, the scope of his secrets, is likely far greater than I can currently imagine. The “hubby’s network logs” are not just a window into his past actions, but a potential roadmap to his future intentions.
The Loneliness of Knowing
The most profound consequence of this discovery is the isolation it has brought. I can’t confide in friends or family without revealing a truth that would undoubtedly cause irreparable damage. I am alone with this knowledge, navigating its treacherous terrain without a guide. The comfort of my shared life has been replaced by the chilling realization that I might be sharing it with a stranger. The network logs were not a tool for understanding; they were a catalyst for profound and disorienting loneliness.
FAQs
What are network logs and how are they used to catch someone?
Network logs are records of the communications that occur within a network, including internet usage, emails, and file transfers. They can be used to track a person’s online activity and can be helpful in catching someone engaging in suspicious or inappropriate behavior.
Is it legal to use network logs to catch someone?
The legality of using network logs to catch someone depends on the specific circumstances and the laws of the jurisdiction in which it is being used. In some cases, employers may have the right to monitor their employees’ network activity, while in other cases, it may be considered an invasion of privacy.
What are the potential consequences of using network logs to catch someone?
Using network logs to catch someone can have various consequences, including legal implications if privacy laws are violated. Additionally, it can have personal and relationship consequences, such as trust issues and damage to the relationship.
What are some signs that someone may be using network logs to catch their spouse?
Signs that someone may be using network logs to catch their spouse include sudden changes in behavior, increased secrecy about their online activity, and unexplained knowledge of their online behavior.
What are some alternative ways to address suspicions in a relationship without using network logs?
Alternative ways to address suspicions in a relationship without using network logs include open and honest communication, seeking counseling or therapy, and setting boundaries and expectations for online behavior within the relationship.