In the realm of digital forensics and scholarly integrity, the question of authorship is paramount. When the authenticity of a written work is called into question, or when subtle traces might point to the original creator, delving into the metadata and remnants left behind by digital devices can offer a powerful, albeit complex, pathway to verification. I’ve found that the seemingly innocuous data generated by our everyday interactions with computers and other electronic tools acts as a digital fingerprint, offering a subtle narrative of creation and usage. This article explores how I, as an author and researcher, leverage device logs for authorship verification.
When I create a document, it’s not just the words that come into being. My computer, the silent scribe, meticulously records a tapestry of information. These are the device logs – the breadcrumbs of my digital activity. They are not designed for public consumption, but rather for the internal workings of the system, for diagnostics, and for tracking user interactions. Think of them as the invisible ink on a historical document, revealing details that the visible text might obscure.
What Constitutes a Device Log?
The scope of device logs is vast, encompassing a spectrum of data. When I consider authorship verification, I’m looking for several key categories:
System Event Logs: The Chronicle of Operations
These logs document the fundamental operations of my computer. They record when applications are launched, when files are accessed, modified, or deleted, and when system services start and stop. For authorship verification, the timestamps and sequence of these events can be incredibly revealing. If a document is claimed to have been written at a certain time, and the system logs show no corresponding activity or a contradictory sequence of events, it casts a long shadow of doubt.
Application-Specific Logs: The Diary of a Program
Many applications maintain their own logs, providing a more granular view of their internal processes. For instance, word processing software might log auto-save events, formatting changes, or even the duration of certain editing sessions. These logs are like the individual author’s private journal, detailing their specific creative journey within a particular tool.
Network Logs: The Trails of Connectivity
While not directly related to document creation, network logs can provide corroborating evidence. They record when my device connected to the internet, which IP addresses it communicated with, and when. If a document is claimed to have been authored at a remote location, I might look for network activity that aligns with that claim, or conversely, evidence of local network access that contradicts it.
Hardware and Driver Logs: The Machine’s Voice
Even the hardware components and their drivers generate logs. These can track device usage, power states, and any errors encountered. While less directly tied to authorial intent, a pattern of hardware usage that aligns with the creation of a document can be a subtle confirmation. For example, consistent use of a specific keyboard or input device might be noted.
In the realm of digital forensics, the use of device logs to establish authorship has gained significant attention, particularly in legal contexts. A related article that delves deeper into this topic can be found at this link. It explores various methodologies for analyzing device logs and how they can serve as crucial evidence in determining the true authors of digital content, thereby enhancing the integrity of digital investigations.
The Art of Extraction and Analysis: Mining for Authorship Clues
Extracting meaningful information from these logs is not akin to plucking ripe fruit from a tree; it’s more like a meticulous archaeological dig. The data is often raw, voluminous, and requires specialized tools and techniques to interpret. My approach involves a systematic process of gathering, filtering, and cross-referencing.
Navigating the Labyrinth of Log Files
The sheer volume and often cryptic nature of log files can be overwhelming. However, understanding the structure and common formats allows for effective navigation.
Locating Essential Log Sources
Different operating systems store their logs in distinct locations. For instance, on Windows, the Event Viewer is a central hub. On macOS and Linux, log files are typically found in directories like /var/log. Identifying these locations is the first step in my investigative process.
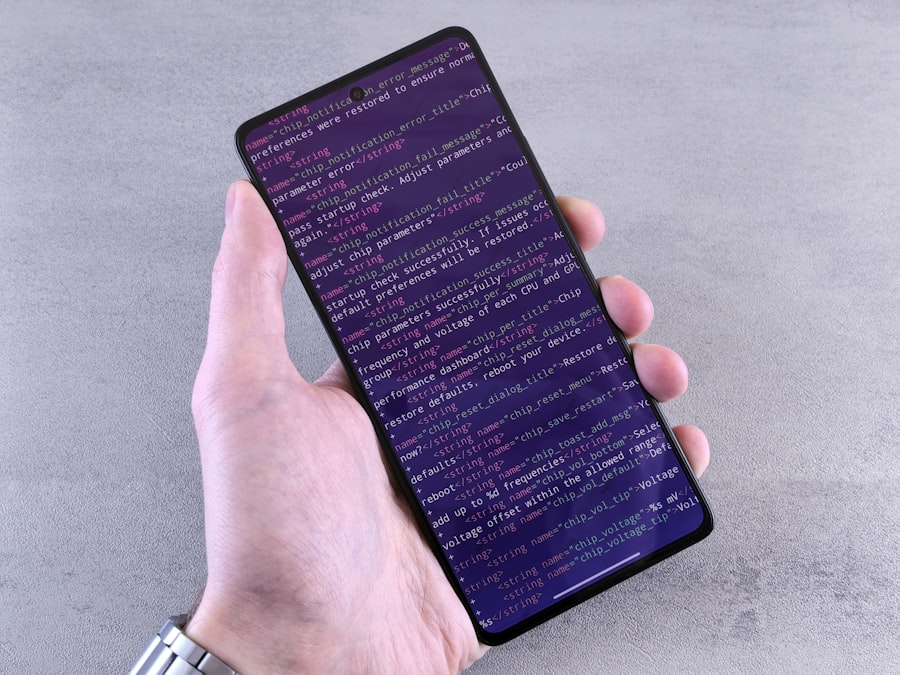
Deciphering Log Formats and Structures
Log files can range from plain text to highly structured formats like JSON or XML. I must be able to read and understand these formats to extract the relevant data points. This often involves using scripting languages to parse and filter the information I need.
Correlating Timestamps: The Backbone of Verification
The timestamps embedded within device logs are the most critical elements for authorship verification. They provide the temporal scaffolding upon which the narrative of creation is built.
Establishing a Timeline of Activity
My primary goal is to build a chronological sequence of events related to the document in question. This involves identifying when the document was created, modified, saved, and potentially accessed by others.
Identifying Anomalies and Inconsistencies
Discrepancies in timestamps are often the red flags that signal potential authorship issues. If the log files suggest a document was accessed or modified at a time when the alleged author claims to have been elsewhere or engaged in entirely different activities, it immediately raises questions. This is like finding a diary entry that clashes with a witness’s sworn testimony.
File System Metadata: The Document’s Birth Certificate
Beyond system logs, the file itself carries its own intrinsic metadata, acting as its birth certificate. This is not external logging, but rather inherent information carried by the file.
Created and Modified Timestamps
Every file has built-in timestamps indicating when it was first created and when it was last modified. While these can be manipulated, they provide a foundational point of reference.
Author and Owner Information
In some file formats, explicit author or owner fields can be present. While these are easily altered, their presence or absence, and the information they contain, can be a contributing factor, especially when cross-referenced with other data.
Revision History and Version Control
If the document was created using software with built-in version control or revision history features, this provides an invaluable layer of detail, tracking changes and attributing them to specific users or sessions.
The Limitations and Nuances: When the Map Isn’t the Territory

While device logs are a powerful tool, it’s crucial to acknowledge their limitations. They are not infallible, and skilled individuals can, to some extent, manipulate or obscure this data. My role is to understand these limitations and to build a case based on the preponderance of evidence, rather than absolute certainty.
The Shadow of Manipulation: Obfuscation and Forgery
The most significant challenge is the potential for logs to be altered or fabricated. Sophisticated individuals can employ techniques to create fake log entries or to delete incriminating ones.
Understanding Log Tampering Techniques
I must be aware of common methods for log tampering, such as editing log files directly, using specialized software to inject false entries, or utilizing system utilities to clear event logs. This awareness allows me to scrutinize the integrity of the logs themselves.
The Importance of Data Integrity and Chain of Custody
When utilizing device logs for verification, maintaining the integrity of the data and ensuring a clear chain of custody is paramount. Any suspicion of tampering necessitates a deeper, more rigorous forensic examination. This is like ensuring the integrity of evidence in a physical crime scene; any mishandling could render it inadmissible.
The Human Element: Interpretation and Context
Logs provide raw data, but interpretation is a human endeavor. The context surrounding the data is as important as the data itself.
The Need for Expert Interpretation
Interpreting complex log data often requires specialized forensic knowledge. A single timestamp or event entry can be misleading if not understood within the broader context of system operations and user behavior.
Social Engineering and Psychological Factors
Sometimes, the analysis of device logs needs to consider social engineering tactics or psychological motivations that might lead to authorship disputes. For example, an individual might claim authorship of a work they did not fully create to gain recognition or financial benefit.
Beyond the Binary: Probabilistic Authorship Verification
Authorship verification using device logs rarely leads to a definitive “yes” or “no” answer. Instead, I often arrive at a probabilistic conclusion – a measure of confidence in a particular attribution. This probabilistic approach mirrors how many scientific and forensic inquiries are conducted.
The Power of Cumulative Evidence
The strength of device log analysis lies in its ability to build a cumulative case. A single log entry might be dismissed, but a consistent pattern of activity that aligns with a specific author’s claimed timeline and methods can be highly compelling.
Building a Profile of the Author’s Digital Habits
By analyzing logs from various documents and periods, I can begin to build a profile of an individual’s digital habits. This includes their preferred software, their typical working hours, their usual file saving locations, and their online activity patterns. When a new document aligns with this established profile, it strengthens the case for their authorship.
Identifying and Acknowledging Counter-Evidence
It’s equally important to identify and acknowledge any counter-evidence that might suggest an alternative authorship or cast doubt on the primary attribution. Dismissing contradictory information would be akin to a detective ignoring clues that point away from their prime suspect.
Statistical Approaches and Machine Learning
In more complex cases, statistical approaches and machine learning algorithms can be employed to analyze large volumes of log data and identify subtle patterns that might escape human observation.
Anomaly Detection and Outlier Identification
Machine learning models can be trained to identify anomalies in log data that deviate from established patterns, which could indicate unauthorized access or manipulation.
Attribution Models Based on Digital Behavior
Advanced models can attempt to attribute documents or digital activities to specific users based on their unique digital behavioral footprints derived from log analysis. This is like a fingerprint analysis, but for digital interactions.
In the realm of digital forensics, the use of device logs has emerged as a crucial method for establishing authorship in various contexts, including legal disputes and academic integrity cases. A fascinating article that delves deeper into this topic can be found at this link, where the author explores how analyzing timestamps and user activity can provide compelling evidence in determining who created a particular piece of content. This approach not only enhances the credibility of claims but also underscores the importance of maintaining accurate logs in our increasingly digital world.
The Future of Authorship Verification: Evolving Technologies and Ethical Considerations
| Metric | Description | Relevance to Proving Authorship | Example Data Points |
|---|---|---|---|
| Timestamp Accuracy | Precision of recorded time for each device action | Helps establish timeline of document creation and edits | Creation time, last modified time, access logs |
| Device Identifier | Unique ID of the device used (e.g., MAC address, device ID) | Links document activity to a specific device | Device serial number, IP address, user account ID |
| User Authentication Logs | Records of user login and logout events | Confirms which user was active during document creation | Login timestamps, user IDs, session durations |
| Application Usage Logs | Logs of software used to create or edit documents | Shows which applications were used and when | App start/stop times, document open/close events |
| File Access Logs | Records of file open, edit, save, and close actions | Tracks interaction with the document over time | File open time, save time, edit count |
| Keystroke and Input Logs | Detailed logs of user input events (if available) | Provides evidence of user activity and authorship patterns | Typing speed, input timestamps, error corrections |
| Network Activity Logs | Records of network connections related to document access | Helps verify remote access or collaboration events | IP addresses, connection times, data transfer logs |
| Metadata Consistency | Comparison of document metadata with device logs | Ensures document metadata matches device activity | Author name, creation date, modification date |
As technology continues to advance, so too will the methods and challenges associated with device log analysis for authorship verification. I anticipate a future where this field becomes even more sophisticated, while also grappling with increasing ethical complexities.
The Rise of Cloud-Based Forensics
With a significant portion of digital activity now occurring in the cloud, the focus of log analysis is shifting. Verifying authorship on cloud platforms presents new challenges and opportunities.
Tracking Activity Across Distributed Systems
Analyzing logs from cloud services requires understanding how data is distributed and how user activity is logged across multiple servers and virtual environments.
The Role of Cloud Provider Logs
Cloud providers maintain extensive logs of user activity, which can be invaluable for authorship verification, although access to these logs often requires legal authorization.
Ethical Implications and Privacy Concerns
The use of device logs for authorship verification raises significant privacy concerns. Accessing and analyzing an individual’s digital footprint, even for legitimate purposes, must be done with utmost care and adherence to ethical guidelines.
The Right to Privacy vs. The Need for Truth
Striking a balance between an individual’s right to privacy and the need to establish authorship and prevent academic or legal misconduct is a constant challenge.
Transparency and Consent in Data Analysis
Whenever possible and appropriate, transparency about data collection and analysis, and obtaining consent for the use of personal device logs, are crucial ethical considerations. This is about ensuring that the search for truth does not trample on fundamental rights.
In conclusion, leveraging device logs for authorship verification is a multifaceted and evolving discipline. It requires a deep understanding of technology, a rigorous analytical approach, and a constant awareness of the inherent limitations and ethical considerations. As I continue to navigate this intricate landscape, I find that the digital dust left behind by our devices, when meticulously examined, can indeed tell a powerful story about who wrote what, and when. It is a testament to the fact that even in the ephemeral world of digital creation, traces remain, waiting to be deciphered.

WATCH NOW ▶️ SHOCKING: One Heart Rate Spike Exposed My Brother’s $2M Fraud
FAQs
What are device logs in the context of proving authorship?
Device logs are records automatically generated by electronic devices that document activities such as file creation, modification times, user access, and application usage. These logs can serve as digital evidence to establish when and by whom a document or file was created or altered.
How can device logs help prove authorship of a document?
Device logs can provide timestamps and user activity data that correlate with the creation or editing of a document. By analyzing these logs, it is possible to verify if a specific user was active on the device at the time the document was created or modified, supporting claims of authorship.
Are device logs considered reliable evidence in legal or academic disputes?
Device logs are generally considered reliable as they are automatically generated and difficult to alter without detection. However, their admissibility and weight as evidence depend on the context, the integrity of the logs, and the ability to authenticate them in legal or academic settings.
What types of device logs are commonly used to prove authorship?
Common types of device logs used include system logs, application logs, file system metadata, and audit trails. These logs record details such as user login times, file access and modification timestamps, and software usage, all of which can help establish authorship.
Can device logs be manipulated, and how can their authenticity be verified?
While device logs can potentially be tampered with, such manipulation often leaves traces or inconsistencies. Authenticity can be verified through forensic analysis, cross-referencing multiple logs, using cryptographic hashes, and employing specialized software tools designed to detect alterations.