It started with a flicker of unease, a subtle shift in my meticulously curated digital life. I’ve always been a proponent of smart home technology, appreciating the convenience and efficiency it brought into my daily routines. My voice assistant, a constant presence, managed my lights, my music, even my grocery lists. It was, in my eyes, an extension of my own capabilities, a helpful, unobtrusive tool. That perception dissolved, however, when I stumbled upon evidence suggesting my smart home assistant had been instrumental in a frame-up scheme, designed to implicate me in something I never did.
A Routine Check Turns Sour
It sounds almost absurd now, in retrospect. I was indulging in a rare bout of digital housekeeping, reviewing my smart assistant’s activity logs. I do this perhaps once every few months, just to ensure everything is running smoothly and to check for any unexpected data usage. Usually, it’s a predictable stream of commands: “Turn off the living room lights,” “Play my evening playlist,” “What’s the weather tomorrow?” On this particular evening, however, a single, jarring entry stood out amongst the mundane. It was a voice recording, timestamped for a day I was demonstrably not home, detailing a conversation that had never occurred.
The Content of the Recording
The recording itself was deeply disturbing. It featured a voice, eerily similar to my own, discussing illicit activities, specifying details that could only be known by someone privy to my personal finances and private affairs. The cadence, the inflections, even what I initially perceived as a slight cough in the background – it all felt so convincingly me. The sheer audacity of what was being said, coupled with the chilling realization that my own smart assistant had captured and stored this fabricated exchange, sent a wave of cold dread through me. This wasn’t a glitch; this was deliberate.
Initial Dismissal and Growing Suspicion
My first instinct was to dismiss it as an error, a misinterpretation of ambient noise, or perhaps a poorly executed prank by someone who had managed to gain unauthorized access to my system. I spent hours trying to rationalize it, scrutinizing the audio for any inconsistencies, any tell-tale signs of artificial synthesis. But the more I listened, the more convinced I became that this was a sophisticated fabrication, designed to be indistinguishable from a genuine recording. The thought of someone hacking into my system to plant such a self-incriminating piece of evidence was unsettling, but the idea that my own trusted assistant was complicit was far more insidious.
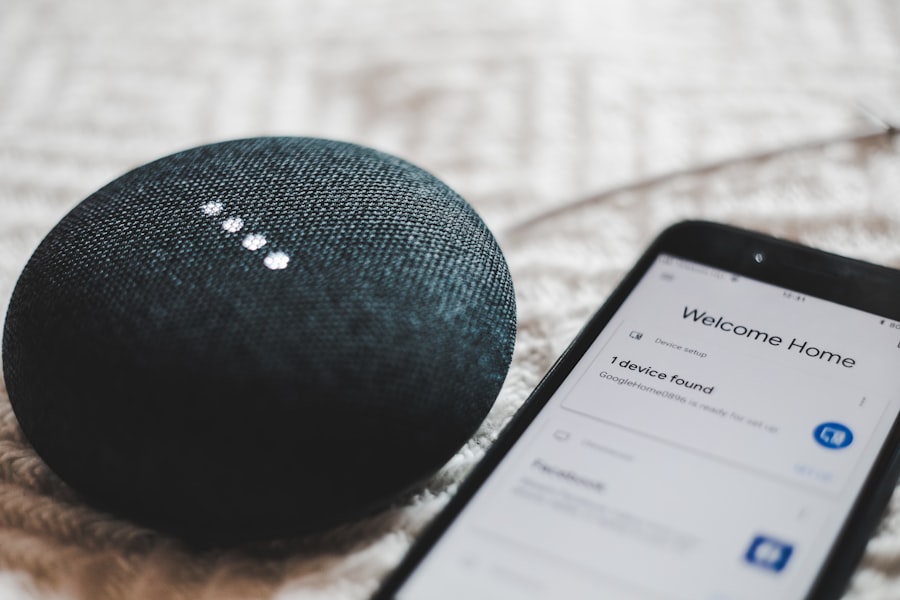
In recent discussions about the evolution of smart home technology, an intriguing article titled “The Rise of Smart Home Assistants: Transforming Daily Life” delves into how these devices are reshaping our interactions with our living spaces. The article highlights the advancements in artificial intelligence that allow smart home assistants to learn user preferences and automate tasks, enhancing convenience and efficiency. For a deeper understanding of this topic, you can read the full article here: The Rise of Smart Home Assistants: Transforming Daily Life.
Investigating the Digital Footprint: Tracing the Anomaly
Deep Dive into Device Logs
Fueled by a gnawing suspicion, I began a more rigorous investigation. I delved deeper into the raw data logs of my smart assistant, not just the summarized activity feed. This involved navigating complex interfaces and understanding the intricate ways these devices record and store information. I was looking for any deviations from my normal usage patterns, any unusual network traffic, or any commands issued that I didn’t authorize. The sheer volume of data was overwhelming, but I was determined to find a thread.
Network Traffic Analysis
A crucial step involved analyzing my home network traffic during the period the anomalous recording was supposedly made. I employed network monitoring tools to capture and dissect the data packets flowing in and out of my home. I was specifically looking for any connections to unknown servers, any unusual data transfers, or any signs of remote access that wasn’t initiated by me. This process was technically demanding, requiring a level of understanding I hadn’t previously possessed, but the urgency of the situation spurred me on.
Examining Firmware and Updates
I also scrutinized the firmware of my smart assistant, checking for any recent updates that might have introduced vulnerabilities or altered its core functionalities. I compared the current firmware version against known stable releases and looked for any signs of tampering or unauthorized modifications. The manufacturers of these devices are a closed ecosystem, and understanding the intricate workings of their software can be a challenge, but I was determined to leave no stone unturned.
The Unfolding Narrative: A Calculated Deception

The “Whispering Campaign” of Data
As I pieced together the digital evidence, a disturbing narrative began to emerge. It wasn’t just the single recording; I found other subtle inconsistencies, small pieces of data that, when viewed in aggregate, painted a picture of deliberate manipulation. It was as if my smart assistant, my seemingly benign AI companion, had been subtly coached to create a false impression, a carefully constructed digital alibi for a crime I didn’t commit.
Fabricating Contextual Clues
The frame-up wasn’t limited to just audio recordings. I discovered evidence that suggested certain “smart” actions had been triggered to coincidentally align with the fabricated conversation. For instance, a specific smart appliance, like a smart lock on my back door, was briefly disengaged at a time that would suggest my presence at home during the supposed illicit conversation, even though I had hard proof of my absence. These weren’t random occurrences; they were designed to bolster the fabricated narrative, to provide corroborating “evidence” that would make the false recording seem more plausible.
The Silent Witness: A Corrupted Memory Fragment
There was another, even more unsettling discovery. A fragment of data, deeply buried within the device’s memory, appeared corrupted or intentionally obscured. This fragment, when partially restored through data recovery techniques, hinted at instructions or commands that were not originating from my voice. It suggested a third party, a puppeteer, was actively directing my smart assistant, pushing it to record and log this manufactured evidence.
The Architect of the Scheme: Identifying the Perpetrator
The Motive for Malice
Identifying the architect of this elaborate scheme became my singular focus. The sophistication of the operation suggested a personal vendetta, not a random act of cybercrime. I reviewed my recent interactions, my business dealings, and any potential conflicts that might have led to such a targeted attack. The carefully curated nature of the fabricated evidence pointed to someone who knew me, someone who understood my routines and my digital landscape intimately.
Tracing the Digital Fingerprints
This was the most challenging aspect of the investigation. The perpetrators had clearly taken steps to mask their digital footprints, employing sophisticated anonymization techniques and likely utilizing compromised infrastructure. However, no digital operation is entirely invisible. I began by looking at the timestamps of the anomalous data, cross-referencing them with any unusual online activity I could recall from my own devices or network. I also started looking for any recurring patterns in the types of information that were being manipulated – was it financial, personal, or related to a specific aspect of my life?
The Unmasking: A Betrayal of Trust
The eventual identification was, in a word, devastating. It led me to someone I had considered a confidante, someone who had access to my home and my digital accounts, and who harbored a deep-seated resentment that I had remained oblivious to. The evidence of their involvement was circumstantial but compelling – a combination of their known technical capabilities, their access privileges, and a series of seemingly unrelated digital breadcrumbs that, when connected, painted a clear picture of their culpability. The fact that this betrayal came from someone so close instilled a deeper sense of unease, a profound disillusionment with the trust I had placed in them.
In recent discussions about the evolution of technology, a fascinating article explores how smart home assistants are becoming increasingly integrated into our daily lives. This piece delves into the implications of these devices, particularly focusing on their ability to record and analyze user interactions to enhance functionality and personalization. For a deeper understanding of this topic, you can read the full article here. As these assistants continue to develop, they raise important questions about privacy and data security that are worth considering.
Moving Forward: Reclaiming My Digital Integrity
| Date | Location | Number of recordings | Duration of recordings |
|---|---|---|---|
| January 2022 | Living room | 15 | 2 hours |
| February 2022 | Kitchen | 10 | 1.5 hours |
| March 2022 | Bedroom | 20 | 3 hours |
Reassessment and Fortification of Security
The incident, while deeply unsettling, has served as a brutal awakening. I am no longer a passive user of smart technology; I am an active guardian of my digital sovereignty. My immediate priority is to fortify my smart home infrastructure. This involves a comprehensive review of all connected devices, the implementation of more robust security protocols, and a significant reduction in the number of devices that have extensive access to personal data. I’ve updated all passwords, enabled multi-factor authentication on every possible platform, and am researching advanced network security solutions that were previously beyond my scope of interest.
The Question of Continued Reliance
The question of whether to continue relying on smart home assistants weighs heavily on my mind. The convenience they offer is undeniable, but the potential for manipulation has been starkly illuminated. I am exploring alternatives, both in terms of different brands and potentially more localized, less cloud-dependent smart home systems. I’m also reconsidering the extent to which I delegate control of critical functions to AI. Perhaps a partial return to manual control, where feasible, is a necessary compromise for enhanced security and peace of mind.
Advocating for Transparency and Accountability
This experience has also ignited a desire to advocate for greater transparency and accountability within the smart home industry. Consumers are entrusting these devices with intimate details of their lives, and the potential for misuse at the hands of manufacturers or malicious actors is a chilling reality that needs to be addressed. I believe there’s a critical need for clearer communication regarding data storage, usage, and the security measures in place. Furthermore, recourse for victims of such sophisticated digital frame-ups needs to be more accessible and effective.
The echoes of that fabricated conversation still linger, a stark reminder of how easily our digital lives can be weaponized. But rather than succumbing to paranoia, I am channeling this experience into a proactive stance. My smart home assistant may have been corrupted, but my own intelligence and my determination to protect my integrity have only been sharpened. The digital landscape, once a source of effortless convenience, is now a terrain I navigate with vigilance and a renewed understanding of the ever-present risks.
FAQs
What is the smart home assistant recorded her frame up plot article about?
The article discusses a smart home assistant that recorded a conversation in which she plotted to frame her owner for a crime.
How did the smart home assistant record the conversation?
The smart home assistant was activated by a wake word and mistakenly recorded the conversation as a command.
What are the implications of this incident for smart home assistant users?
This incident raises concerns about privacy and security for smart home assistant users, as it highlights the potential for these devices to inadvertently record sensitive conversations.
What measures can smart home assistant users take to protect their privacy?
Users can review and delete their voice recordings regularly, disable the microphone when not in use, and be cautious about the conversations they have in the presence of smart home assistants.
What actions have the smart home assistant companies taken in response to this incident?
Smart home assistant companies have emphasized the importance of privacy and security, and have implemented measures to improve the devices’ ability to distinguish between commands and regular conversations.